Find the breach point before it finds you
Our comprehensive guide to strategies for entrepreneurs and leaders offers valuable insights, practical advice.

An AI Offensive Security Engine
Chariot combines Agentic AI, Workflow Automation, and Offensive Capabilities with our veteran team of offensive security engineers. Together, they identify your exploitable vulnerabilities and guide their remediation before threat actors can abuse them.
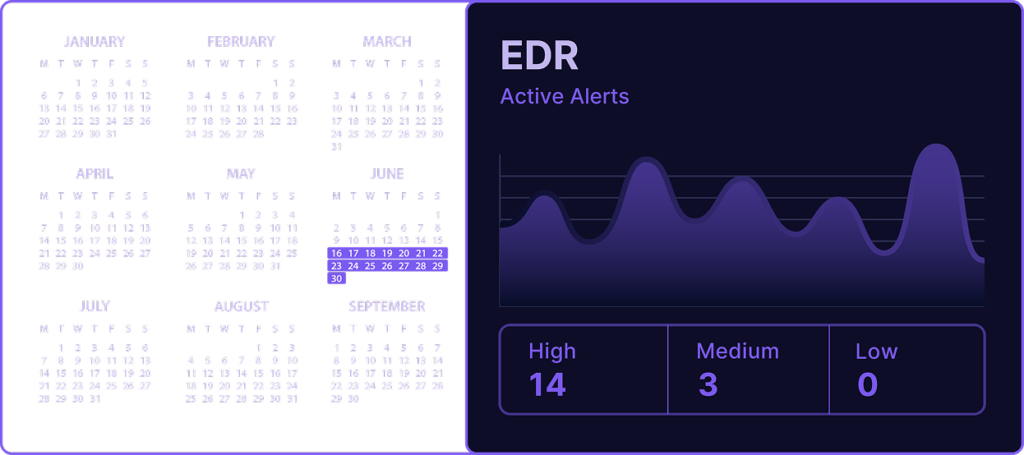
You’d Never Run an EDR 2 Weeks out of the Year
Why are you running offensive security that way?
Stop the Bleeding
Slash Cost, Noise and Misspent Time Now
Reduce Cost
25-50% spend reduction by consolidating ASM, VM, CTI, BAS, and Annual Penetration Tests into a single Platform
Save Time
50-70% reduction of non-needling moving remediation activity
Eliminate Noise
70% faster MTTR; critical vulns validated or closed in record time with a trusted 3rd party guiding and verifying remediation
Satisfy Compliance
100% annual penetration test requirement satisfiaction for FDA, GLBA, HIPPA, NERC, NYDFS, MAS TRM, & PCI‑DSS
Build Immunity
Continuously Strengthen Your Security Posture Over Time
“By 2026, organizations that prioritize their security investments based on a continuous exposure management program will be 3x less likely to suffer a breach.”
Attack Surface Management
Gain comprehensive visibility and control over your rapidly evolving threat landscape through continuous discovery, monitoring, and remediation of material risk found within your evolving attack surface.
Vulnerability Management
Scan for vulnerabilities across your perimeter, cloud environments, on-premise infrastructure, and developer code.
Cyber Threat Intelligence
Enrich vulnerabilities with cyber threat and exploit intelligence as part of our emergent threat monitoring.
Attack Path Mapping
Visualize potential attack paths within your network, helping you to understand how vulnerabilities can be exploited.
Continuous Penetration Testing
Proactively validate the effectiveness of your security controls, simulate real-world attacks, and receive actionable insights to protect against emerging threats.
Breach & Attack Simulation
Put your security controls to the test through simulated real-world attack behaviors against your systems. Identify security gaps, validate defense effectiveness, and optimize your security strategy.
What Customers are Saying
- 21st Century Fox
- Samsung
- Priceline
- X
21st Century FoxSamsungPricelineX
Our team has been able to expand their understanding and their thoughts around how the attacker might come after us. We’ve been able to shift our processes and our technology in response.
We chose Praetorian primarily for the domain expertise, which is IoT in our case, and the security expertise in general.
A lot of this [public cloud] technology was new to us. Praetorian was there as we did those migrations. Praetorian helped us design our cloud security framework, and helped us with the testing along the way.
From the get go Praetorian had a great process in place that kept the X (Twitter) team informed and filled in what to expect. The issues found will help prevent any loss in trust in the product. Looking forward to many more engagements!
Prevention first strategy under one unified platform.
Leverage continuous offensive security to ensure your next hour—and next dollar—are spent on breachable risk.