When Proxies Become the Attack Vectors in Web Architectures
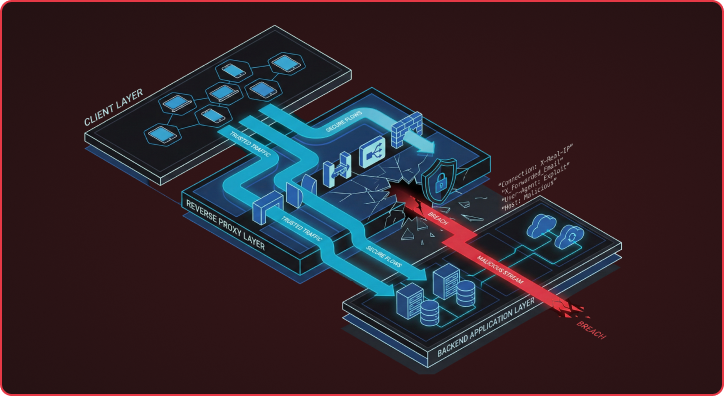
Many Reverse proxy attack vectors expose a flawed assumption in modern web architectures that backends can blindly trust security-critical headers from upstream reverse proxies. This assumption breaks down because HTTP RFC flexibility allows different servers to interpret the same headers in fundamentally different ways, creating exploitable gaps that attackers are increasingly targeting. I want to […]
Your Vulnerability Scanner Might Be Your Weakest Link
Overview Vulnerability scanners are a cornerstone of modern security programs, helping teams identify weaknesses before attackers do. But when these tools are configured with privileged credentials, they can themselves become high-value targets. In one case, while running continuous testing through our Chariot platform for a Fortune 500 financial services company, we compromised a server and […]
The Security Time Capsule: Evolving Beyond Legacy Pen Testing

Legacy point-in-time penetration testing started in the 1960s, back when networks were static, attackers behaved like hobbyists, and change moved slowly. We live in a very different world now. The practice of annual testing was shaped for a world that no longer exists, one without dynamic cloud infrastructure, identity sprawl, or AI-accelerated threats. Yet many […]
Hunting for Secrets in Plain Sight: Leveraging Internal Logging and Monitoring Services
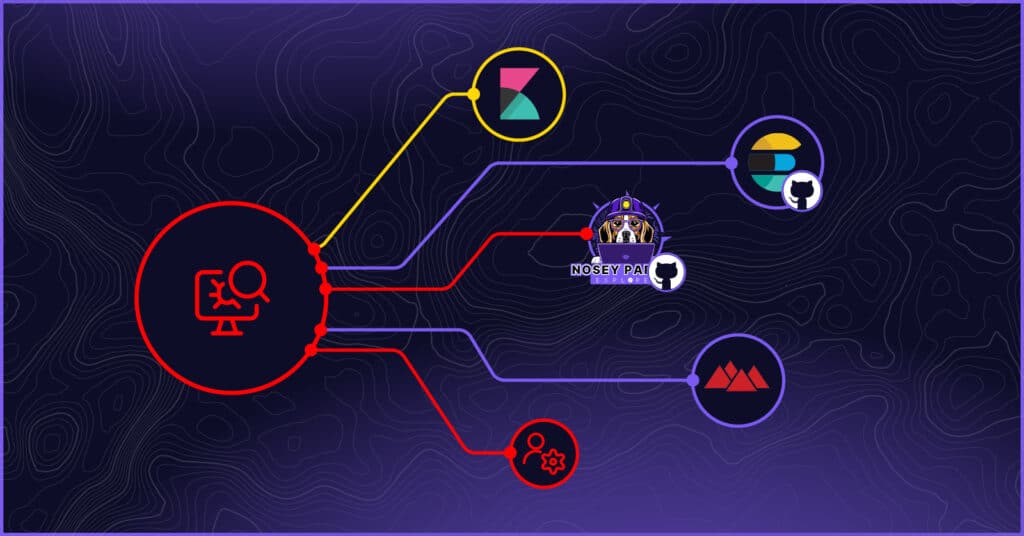
In penetration testing and red teaming, success often lies in uncovering hidden paths of least resistance. While sophisticated exploits and zero-days frequently capture headlines, highly effective attack opportunities often hide in plain sight – like within internal logging and monitoring platforms. At Praetorian, we’ve observed first-hand the value of targeting internal logging and monitoring platforms […]
Leveraging Microsoft Text Services Framework (TSF) for Red Team Operations
The Praetorian Labs team was tasked with identifying novel and previously undocumented persistence mechanisms for use in red team engagements. Our primary focus was on persistence techniques achievable through modifications in HKCU, allowing for stealthy, user-level persistence without requiring administrative privileges. Unfortunately, while we identified an interesting persistence technique, the method we discuss in this […]
Long Live the Pwn Request: Hacking Microsoft GitHub Repositories and More
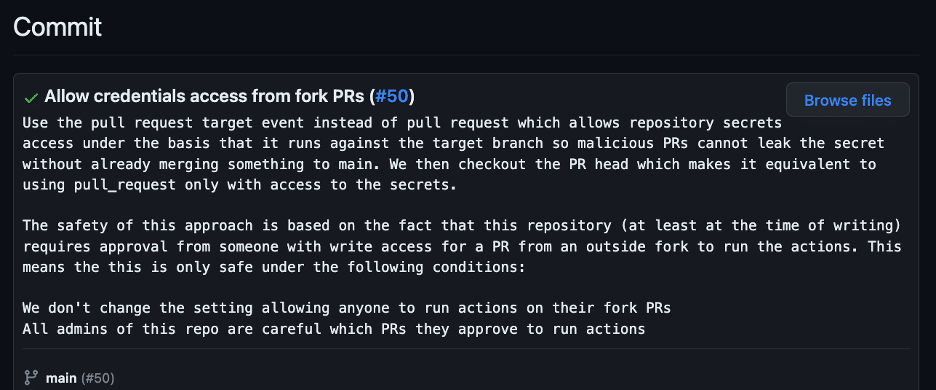
Software supply chain attacks have been increasing both in frequency and severity in recent months. In response to these attacks, the CISA has even released a cybersecurity information sheet (CSI) on how organizations can secure their CI/CD pipelines. The introduction to the CSI states: “(The) CSI explains how to integrate security best practices into typical […]
Helpdesk Telephone Attack: How to Close Process and Technology Gaps
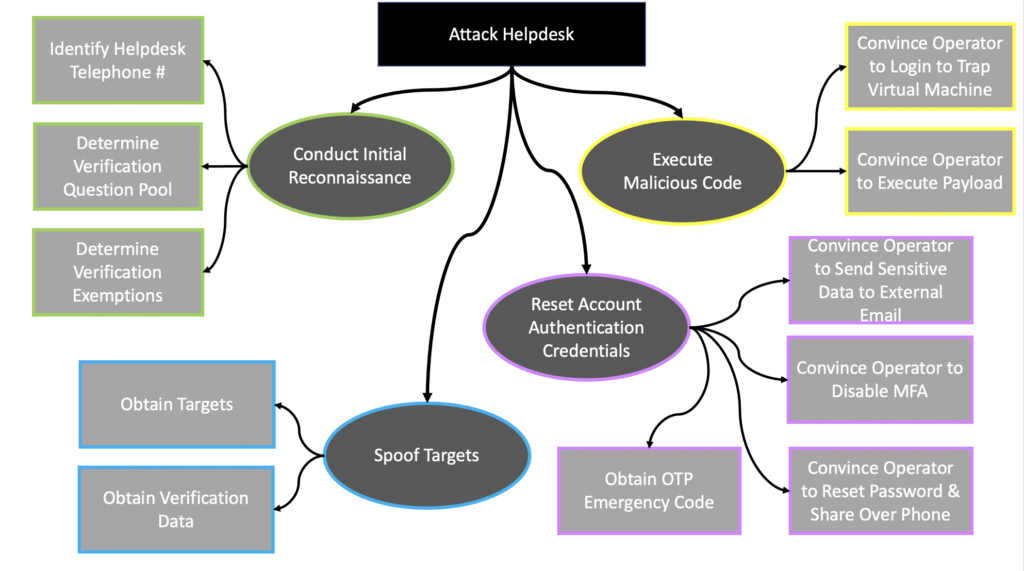
Introduction As we have witnessed in recent weeks with the MGM and Caesars Entertainment breaches, helpdesks are prime attack surfaces that are seeing a surge in exploitation. Although much of the press surrounding these most recent events alludes to helpdesk operators’ roles in the exploits, this type of vulnerability actually is a technology and process […]
Developing a Hidden Virtual File System Capability That Emulates the Uroburos Rootkit

A few years ago, I read the “Uroburos: The Snake Rootkit” [1] paper written by Artem Baranov and Deresz and was captivated by the hidden kernel-mode Virtual File System (VFS) functionality implemented within Uroburos. Later, I decided to learn Windows device driver programming and thought replicating this functionality within my own rootkit would be an […]
Computer Account Relaying Vulnerabilities Part 2
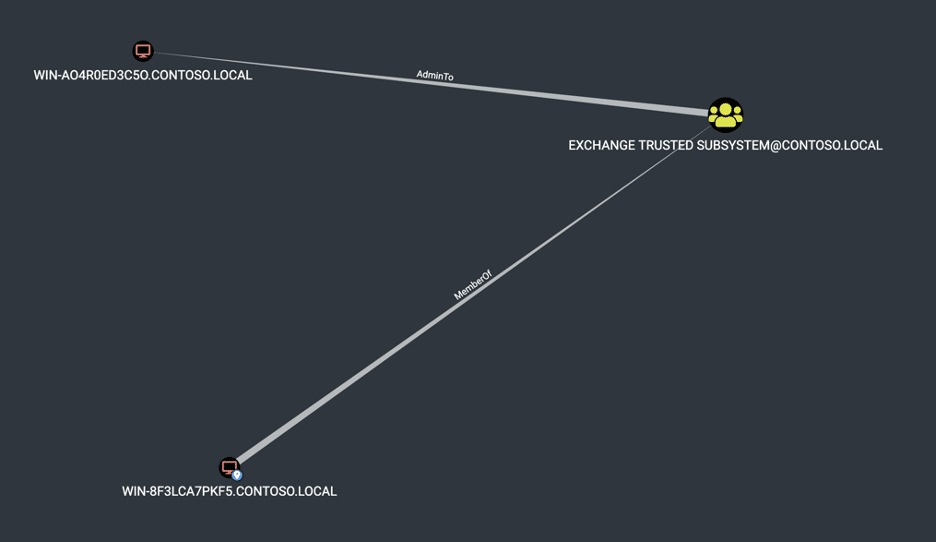
Overview Recently I’ve been working on writing a custom SMB client that implements the initial handshake and NTLM authentication functionality to perform port fingerprinting within Chariot Identify, our attack surface management product. While reading through the SMB specification, I got to thinking about Computer AdminTo Computer vulnerabilities we have exploited over the last few years […]
Spring Core on JDK9+ is vulnerable to remote code execution

Update: March 31, 2022 A patch has officially been released. https://spring.io/blog/2022/03/31/spring-framework-rce-early-announcement https://tanzu.vmware.com/security/cve-2022-22965 Overview Spring Core on JDK9+ is vulnerable to remote code execution due to a bypass for CVE-2010-1622. At the time of writing, this vulnerability is unpatched in Spring Framework and there is a public proof-of-concept available. As we have remediation advice for customers […]