How To Identify and Prevent Query and Command Injections (Part 1)

Query and command injections are some of the most devastating classes of vulnerabilities in existence. This series of blog posts will teach you how to identify and prevent this vulnerability from occurring. In part one we will explore examples of command injection.
Develop Secure Mobile Apps by Studying Vulnerable Android, iOS, and Mobile Web Apps
In today’s mobile world, demand for high-quality, feature-rich applications is increasing, while mobile app development cycles are becoming shorter. With time-to-market pressures greater than ever, security vulnerabilities are manifesting themselves in every stage of the mobile app development life cycle. For our summer internship project, we wanted to come up with a way to help developers create more secure mobile apps.
NECCDC Red Team: Quick Twitter Command and Control (C2) Trojan
In the last few posts I covered a few C2 Trojans (DNS C2 Trojan, HTTP GET and POST Trojan). In this post I wanted to cover a method that uses Twitter for command and control.
NECCDC Red Team: Quick HTTP Command and Control (C2) Trojans
In my previous blog post, I described the Northeast Cyber Collegiate Defense Competition (NECCDC) and started to explain some of the techniques the red team used. For this post, I’m going to cover two more C2 Trojans that I wrote using HTTP (GET and POST). Similar to the C2 DNS Trojan, the HTTP Trojans are unidirectional and do not require installing software on the victim. By using multiple techniques at varying frequency we increased the likelihood we would be able to maintain persistence throughout the competition.
NECCDC Red Team: Quick DNS Command and Control (C2) Trojan
Recently, I had the opportunity to participate in the Northeast Cyber Collegiate Defense Competition (NECCDC) at the University of Maine. The competition was made up of 10 student groups (blue teams) from various colleges in the region that were tasked with protecting a mock network against a group of professional pentesters (the red team) who were trying to break in. This was my third year on the red team. Prior to the competition, I built several tools that would make life easier for the red team and enable us to differentiate between the qualities of the blue teams we were attacking. I am planning to release the code that I built for the competition over the next few months in a series of blog posts.
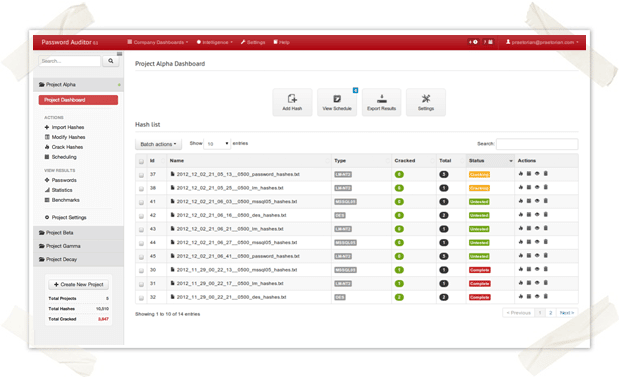
Metasploit Integration for Password Auditor
Last week I introduced our new Password Auditor, an internal project I’m working on here at Praetorian. Today, I’m back with a followup screencast that demonstrates one of its major features — Metasploit integration! If you missed the previous screencast, I recommend watching it to get a sense of the tool’s basic functionality.
Password Auditing with Style
In my last post, I announced that our team has been developing an easy-to-use password cracking tool with advanced features. Our initial goal for the project was to create something that made password auditing easier for our services team. However, after several internal discussions we’ve decided to share our work with the security community in order to see if this tool has value beyond what we had initially envisioned. We’ve even talked about opening up a private, invite-only Beta to let others get some hands-on time with the tool. I encourage you to learn more about the tool and leave feedback/comments below (it may increase your chances of receiving an early invitation).
Easy to Use Password Cracking Tool with Advanced Features
Looking back over this past year, I have noticed a continuing theme among public security breaches. Similar to 2011, this year’s high profile security breaches often end in a public dump of confidential victim data. It is not uncommon for Hacktivist groups, such as Anonymous, to publically dump password hashes and other confidential data as a way of proving the breach occurred and as a way of embarrassing the victim.
Burp SQLmap plugin for Windows

Burp Suite provides a very basic SDK known as Burp Extender. Burp Extender allows third parties to extend the features of an already powerful web application testing suite. In March of this year, Daniel Garcia (cr0hn) created a SQLmap plugin for Burp using the Burp Extender SDK. With Daniel’s SQLmap plugin, automated SQL injection discovery and exploitation is now seamless between two of our favorite web application pentesting tools.
Multi-Core and Distributed Programming in Python
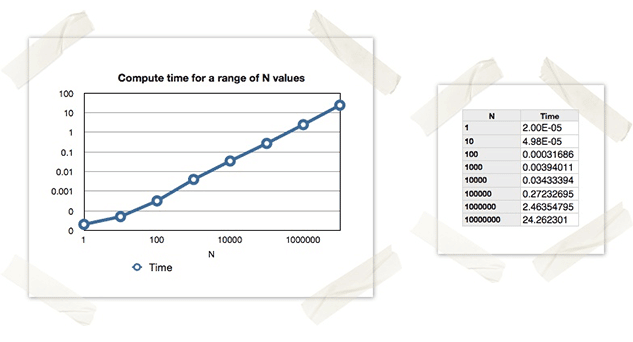
In the age of big data we often find ourselves facing CPU-intensive data processing tasks, therefore it is useful to understand how to harness all available CPU power to tackle a particular problem. Recently we came across a Python script which was CPU-intensive, but when the analyst viewed their overall CPU usage it was only showing ~25% utilization. This was because the script was only running in a single process, and therefore only fully utilizing a single core. For those of us with a few notches on our belts, this should seem fairly obvious, but I think it is a good exercise and teaching example to talk about the different methods of multi-core/multi-node programming in Python. This isn’t meant to be an all-encompassing tutorial on multi-core and distributed programming, but it should provide an overview of the available approaches in Python.