Update: We posted a demo and more information about our new tool!
Later this week we will be introducing a new project and will be reaching out to the community for feedback — Stay tuned.
Looking back over this past year, I have noticed a continuing theme among public security breaches. Similar to 2011, this year’s high profile security breaches often end in a public dump of confidential victim data. It is not uncommon for Hacktivist groups, such as Anonymous, to publically dump password hashes and other confidential data as a way of proving the breach occurred and as a way of embarrassing the victim. This year alone, LinkedIn, Yahoo, and Twitter have all suffered from similar fates. Hacktivist groups will typically upload stolen password hashes to public websites such as pastebin or nopaste for anyone in the world to crack. Once the password hashes fall into public domain, victim organizations must assume the worst case scenario – complete compromise of account credentials. Password cracking tools, with enough time and power, can crack any hash.
From a practicality standpoint, this must occur within a reasonable amount of time and with a reasonable amount of resources. Unfortunately, given today’s computational power, the pervasiveness of weak password policies, and poor password choices by users, most password hashes are, in fact, crackable. Recently, our team has been working on a project that assists in underscoring this risk through an easy to use password cracking tool with advanced analytical capabilities for auditing and training purposes.
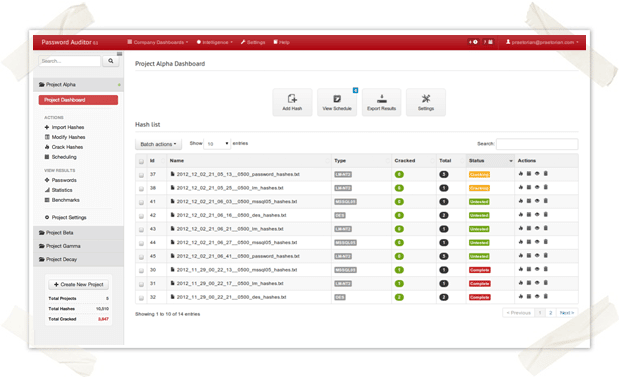
A glimpse of the tool is shown in the screenshot below. We’ll be releasing a full demo in the coming days, so stay tuned!
Update: We posted a demo and more information about our new tool!
