Google Cloud Platform (GCP) Service Account-based Privilege Escalation paths
This article examines a Google Cloud Platform (GCP) risk scenario, in which a malicious user can use their privileges in a compromised service to further escalate their privileges.
NIST Cybersecurity Framework Vignettes: Broadcast Name Resolution Poisoning
Our NIST Cybersecurity Framework Vignettes series focuses on the best applications of NIST CSF for your organization. This article addresses the tactic of Broadcast Name Resolution Poisoning.
NIST Cybersecurity Framework Vignettes: Phishing
This article examines the application of the NIST Cybersecurity Framework for addressing phishing concerns.
Attacking and Defending OAuth 2.0 (Part 1 of 2: Introduction, Threats, and Best Practices)

First of a two-part series discussing OAuth 2.0 from the perspective of a security engineer in both an offensive and defensive role
Active Directory Computer Account SMB Relaying Attack

This article outlines a unique Active Directory attack vector that arises when a computer account has administrative access to another computer.
Cloud Security and Architecture: The 8 Pillars

Praetorian has created a 8-pillar framework to simplify the assessment of multi-cloud environments across a broad client base. Together with proven methodologies for enterprise and product security, the framework provides a holistic approach to securing organizations from chip to cloud.
AWS IAM Assume Role Vulnerabilities Found in Many Top Vendors

Research by Praetorian has uncovered a common misconfiguration in Amazon Web Services Identity and Access Management Assume Role process. This post outlines the issue and how it can be mitigated.
What is Threat Modeling, and Why it’s Important

What is Threat Modeling, why it’s valuable to organizations, and when it should be used?
10 Cybersecurity Technical Priorities for Telework
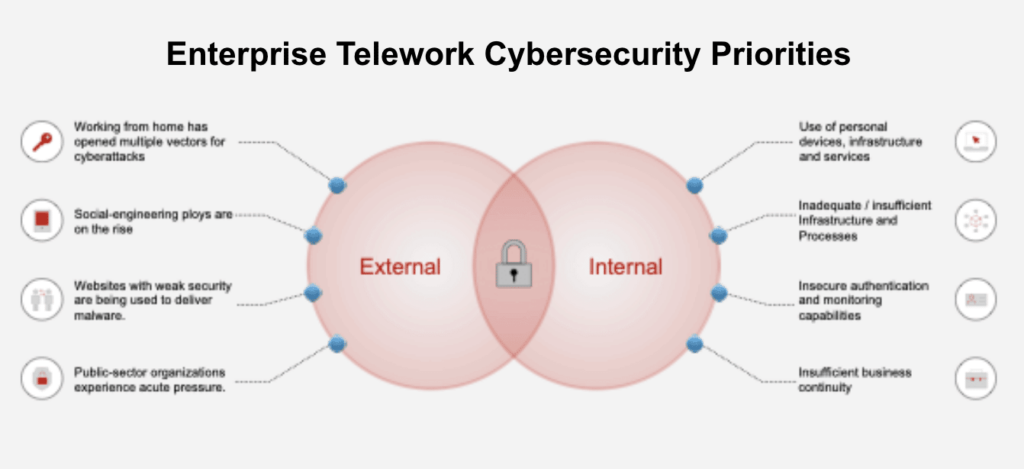
As Telework becomes a new normal, cybersecurity professionals must consider the greater attack surface. This article suggests the top focus areas for consideration.
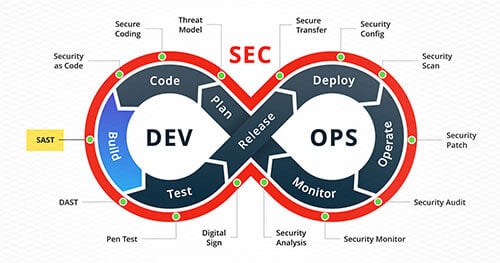
Evaluating SAST Tools
In this article, we aim to provide guidance for organizations that have decided to integrate a SAST tool into their CI/CD pipeline and outline important things to consider before acquiring one.