Adversarial Oracles: LLM-Guided EDR Signature Reduction
In previous blog posts we’ve talked about getting nerd sniped. Today we’re going to talk about a kind of nerd sniping that any offensive security tool creator is familiar with; when your tool gets signatured. This normally kicks off a frustrating spiral of back and forth changes between the tool author and security vendors until […]
Your Login Page Is Lying: What AI Agents Find When They Read Your Frontend
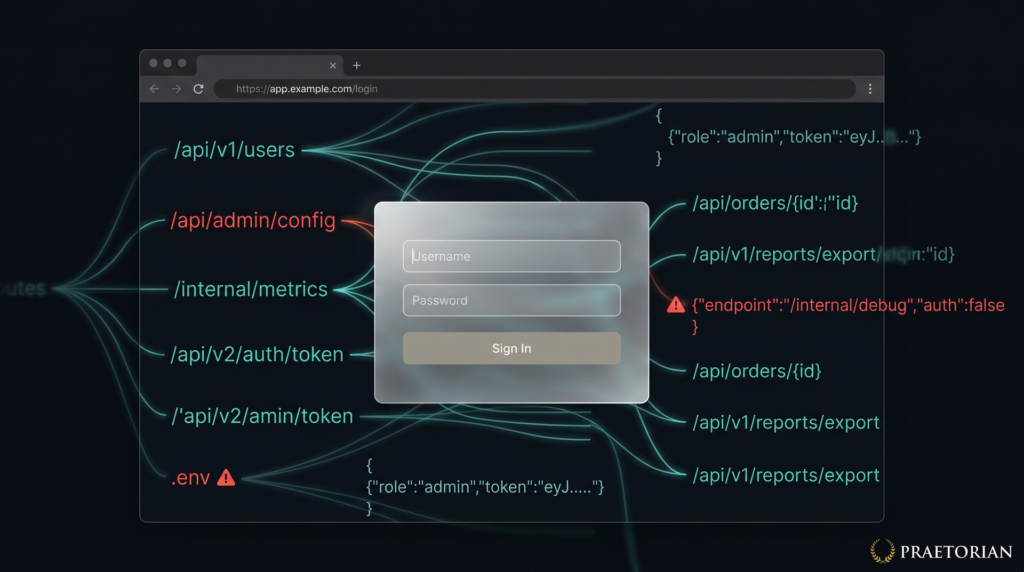
TL;DR: Single-page applications ship their entire frontend codebase to every visitor, including unauthenticated ones. Even a login page with no visible functionality delivers JavaScript bundles containing route definitions, API endpoint URLs, authentication logic, data models, and sometimes hardcoded secrets. As part of Guard’s continuous penetration testing, we use AI-assisted tooling to extract this information and […]
Which Came First: The System Prompt, or the RCE?

During a recent penetration test, we came across an AI-powered desktop application that acted as a bridge between Claude (Opus 4.5) and a third-party asset management platform. The idea is simple: instead of clicking through dashboards and making API calls, users just ask the agent to do it for them. “How many open tickets do […]
Mapping the Unknown: Introducing Pius for Organizational Asset Discovery
Asset discovery is an essential part of Praetorian’s service delivery process. When we are engaged to carry out continuous external penetration testing, one key action is to build and maintain a thorough target asset inventory that goes beyond any lists or databases provided by the system owner. Pius is our open-source attack surface mapping tool […]
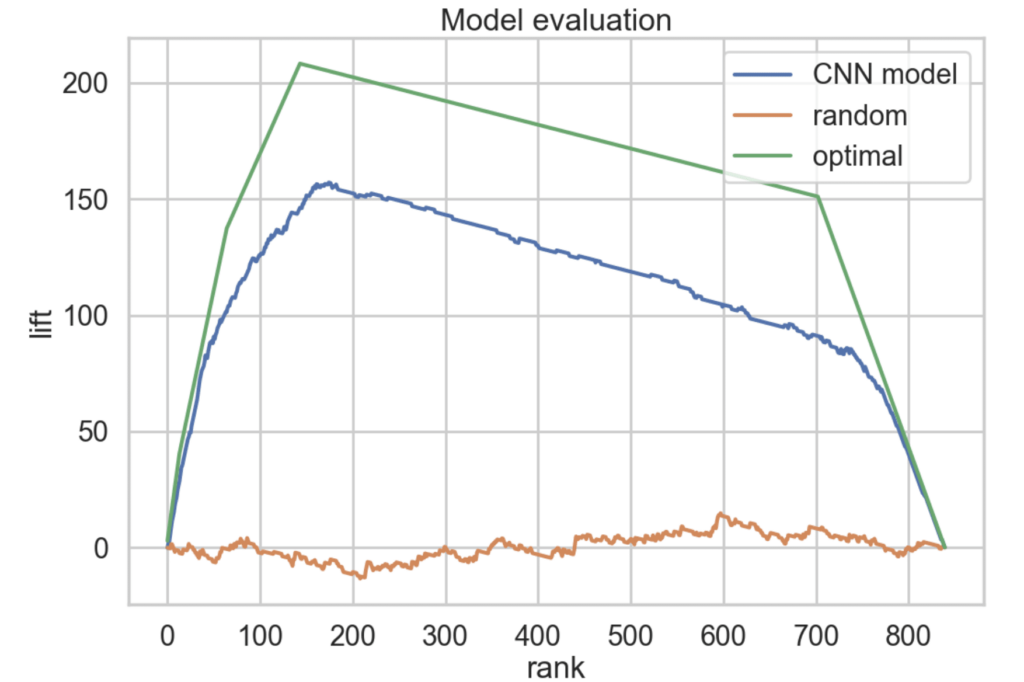
Content Discovery: Understanding Your Web Attack Surface
Attack Surface Management (ASM) tools find quite a lot of vulnerabilities on the Web. This really isn’t surprising, given that HTTP/S is by far the most common and broadest of all the services comprising the Internet. In fact, Web-based issues represent the majority of the findings about which our Managed Service Providers (MSPs) inform our […]
Screenshotting: Can You See What I See?
At Praetorian, we firmly believe that the most effective way to secure your systems is to look at them through an offensive lens. After all, when you view yourself the same way an attacker does, you get a better understanding of which defenses are likely to be effective. When building Chariot, our External Attack Surface […]
Phantom of the Pipeline: Abusing Self-Hosted CI/CD Runners
Introduction Throughout numerous Red Teams in 2022, a common theme of Source Control Supply Chain attacks in GitHub repositories has emerged. After many hours manually hunting for and exploiting these attack paths, we’ve built an all-in-one toolkit called Gato (Github Attack Toolkit) for finding and attacking repositories where these misconfigurations are present. We released the […]
From Self-Hosted GitHub Runner to Self-Hosted Backdoor
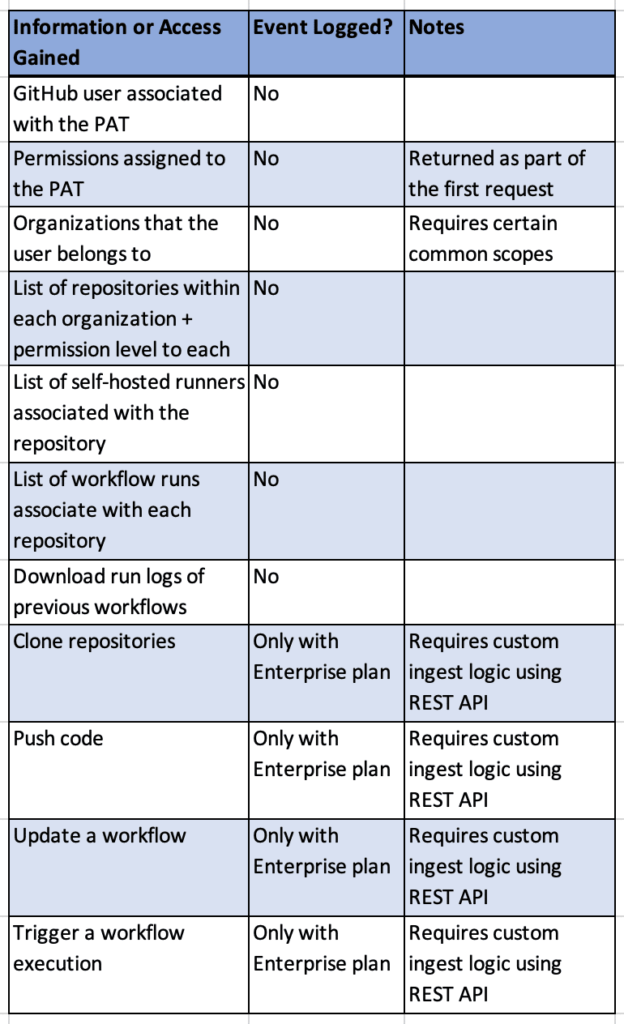
Overview Continuous Integration and Continuous Delivery (CI/CD) systems are powerful and configurable tools within modern environments. At Praetorian, we are seeing organizations migrate to SaaS solutions like GitHub (GitHub.com) as their source code management and CI/CD solution, instead of on-premises tools like BitBucket, Bamboo, and Jenkins. On our Red Team engagements , we routinely employ […]
Developing a Hidden Virtual File System Capability That Emulates the Uroburos Rootkit

A few years ago, I read the “Uroburos: The Snake Rootkit” [1] paper written by Artem Baranov and Deresz and was captivated by the hidden kernel-mode Virtual File System (VFS) functionality implemented within Uroburos. Later, I decided to learn Windows device driver programming and thought replicating this functionality within my own rootkit would be an […]
NTLMv1 vs NTLMv2: Digging into an NTLM Downgrade Attack
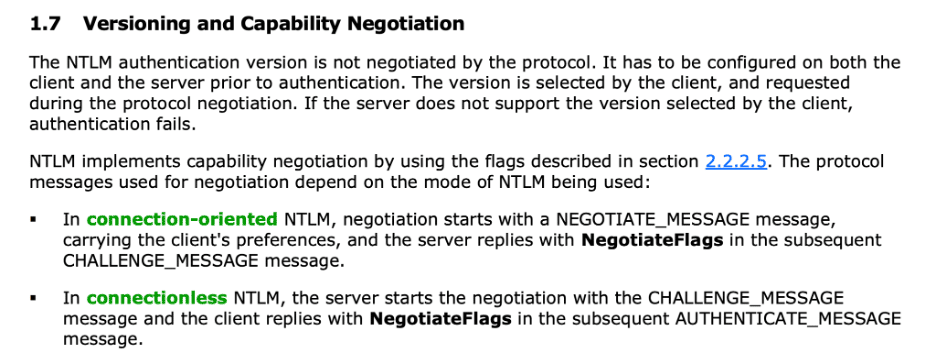
Overview During the summer, my colleague Derya Yavuz and I published an article on some of the different methods we’ve leveraged to elevate privileges within Active Directory environments. We discussed authentication coercion techniques such as PrinterBug, PetitPotam, and DFSCoerce. One of the techniques we mentioned in that article was performing an NTLM downgrade attack to […]