500,000 Vulnerabilities, 14 That Matter: How Exploit Chain Analysis Cuts Through the Noise

When 500,000 Findings Hide 14 Real Threats Modern enterprises ingest vulnerability data from dozens of sources: endpoint detection and response platforms, vulnerability scanners, cloud security posture tools, container image scanners. A large organization can easily accumulate hundreds of thousands of individual findings. The standard response is to sort by CVSS score, filter for criticals, and […]
CVE-2026-3630: Critical Buffer Overflow in Delta Electronics COMMGR2 Enables Remote Code Execution
Key Takeaways CVSS v3.1 base score of 9.8 (Critical) with vector CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H, according to the CNA Delta Electronics COMMGR2 contains an out-of-bounds write vulnerability (CWE-787) enabling unauthenticated remote code execution NVD lists the vulnerability as analyzed; vendor advisory Delta-PCSA-2026-00005 is available addressing multiple COMMGR2 vulnerabilities No evidence of active exploitation in the wild; specific affected […]
When HttpOnly Isn’t Enough: Chaining XSS and GhostScript for Full RCE Compromise
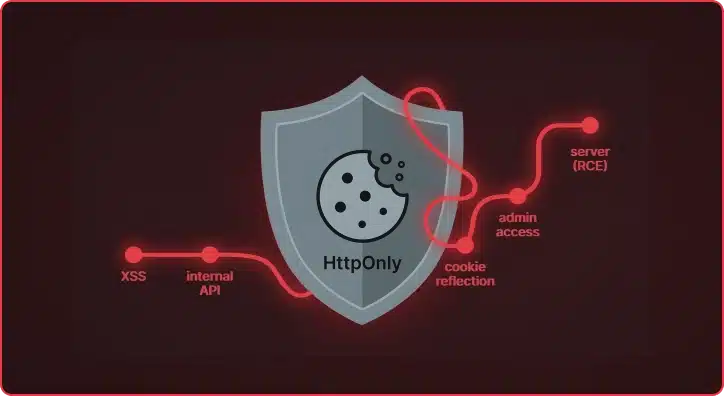
What started as a standard cross-site scripting vulnerability in a document processing platform turned into a full administrative takeover of the application and, ultimately, remote code execution on the underlying server. The HttpOnly flag protected the session cookie from Javascript, but did the application keep it safe? During a recent assessment of a document processing […]
Et Tu, RDP? Detecting Sticky Keys Backdoors with Brutus and WebAssembly

Everyone knows that one person on the team who’s inexplicably lucky, the one who stumbles upon a random vulnerability seemingly by chance. A few days ago, my coworker Michael Weber was telling me about a friend like this who, on a recent penetration test, pressed the shift key five times at an RDP login screen […]
When Proxies Become the Attack Vectors in Web Architectures
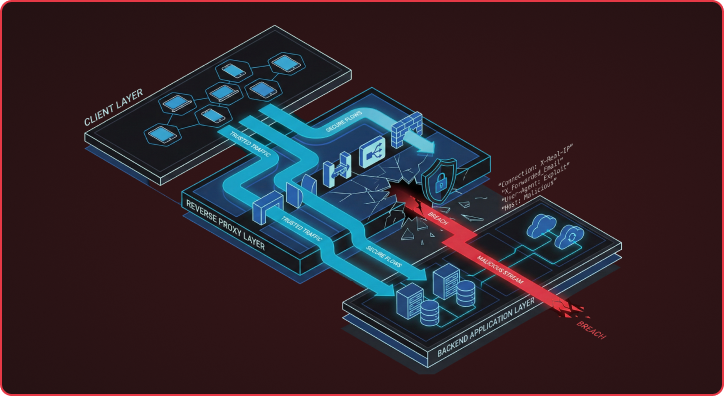
Many Reverse proxy attack vectors expose a flawed assumption in modern web architectures that backends can blindly trust security-critical headers from upstream reverse proxies. This assumption breaks down because HTTP RFC flexibility allows different servers to interpret the same headers in fundamentally different ways, creating exploitable gaps that attackers are increasingly targeting. I want to […]
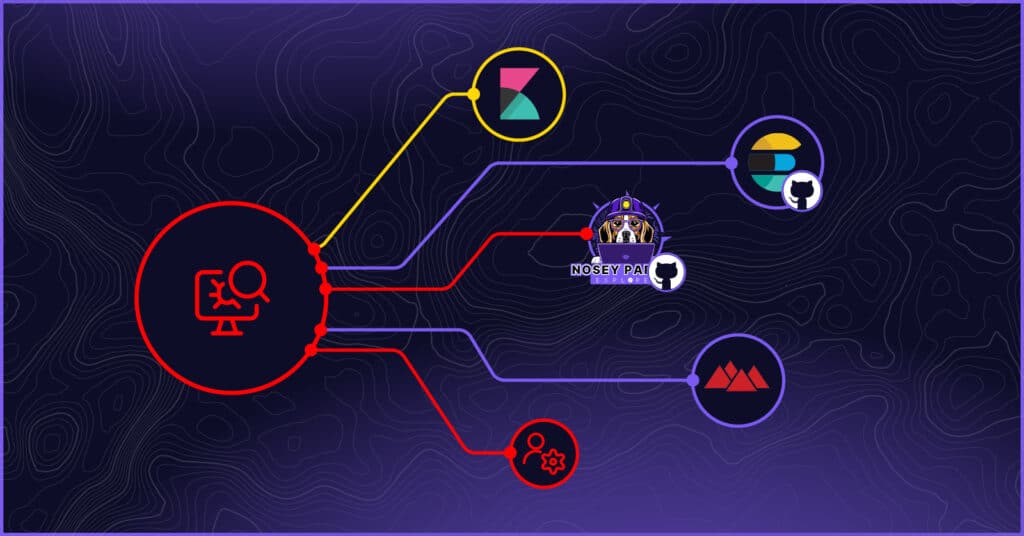
There’s Always Something: Secrets Detection at Engagement Scale with Titus
TL;DR: Titus is an open source secret scanner from Praetorian that detects and validates leaked credentials across source code, binary files, and HTTP traffic. It ships with 450+ detection rules and runs as a CLI, Go library, Burp Suite extension, or Chrome browser extension — putting secrets detection everywhere you already work during engagements. Say you find […]
Hunting for Secrets in Plain Sight: Leveraging Internal Logging and Monitoring Services
In penetration testing and red teaming, success often lies in uncovering hidden paths of least resistance. While sophisticated exploits and zero-days frequently capture headlines, highly effective attack opportunities often hide in plain sight – like within internal logging and monitoring platforms. At Praetorian, we’ve observed first-hand the value of targeting internal logging and monitoring platforms […]
Agent of Chaos: Hijacking NodeJS’s Jenkins Agents
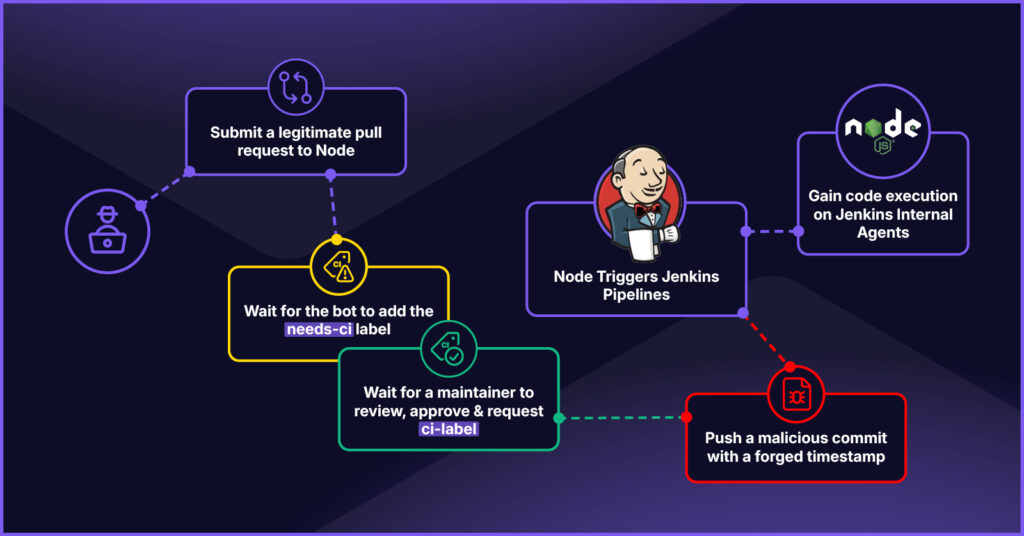
Relationships are complicated. When multiple DevOps platforms work together to execute pipelines for a single GitHub repository, it begs the question: Do these platforms get along? Node.js, the most popular JavaScript runtime in the world, uses a set of triplets to execute its CI/CD pipelines: a GitHub App, GitHub Actions workflows, and Jenkins pipelines. Like […]
ELFDICOM: PoC Malware Polyglot Exploiting Linux-Based Medical Devices
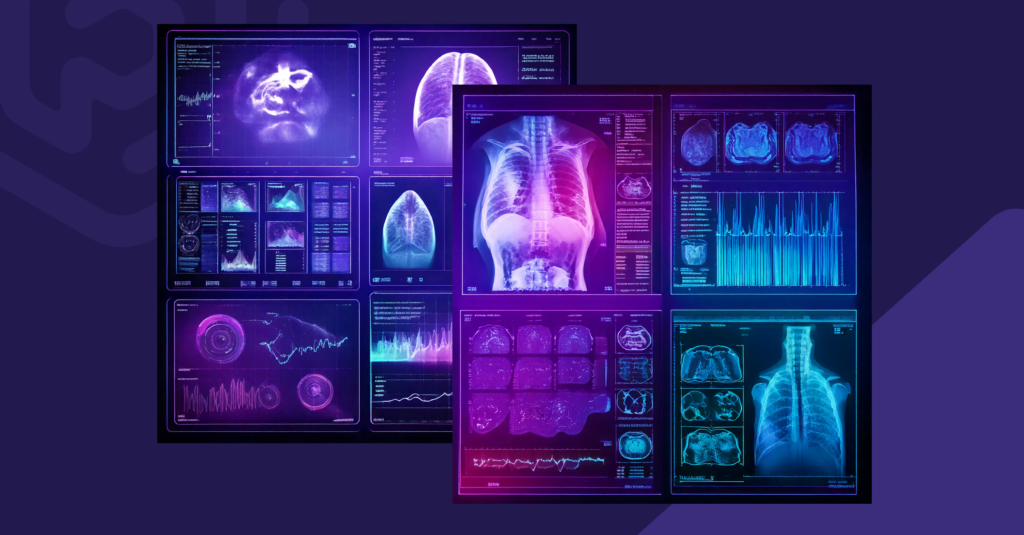
A high severity vulnerability in DICOM, the healthcare industry’s standard file protocol for medical imaging, has remained exploitable years after its initial disclosure. The flaw enables attackers to embed malicious code within legitimate medical image files. While previous research demonstrated this vulnerability’s impact on Windows-based medical systems, Praetorian’s new proof of concept, ELFDICOM, extends the […]
An Improved Detection Signature for the Kubernetes IngressNightmare Vulnerability

Wiz recently published a detailed analysis of a critical vulnerability in the NGINX Ingress admission controller—what they’ve dubbed IngressNightmare (CVE-2025-1097, CVE-2025-1098, CVE-2025-1974, CVE-2025-24514). The vulnerability stems from insufficient input validation during configuration file processing, allowing an attacker to inject arbitrary code into the NGINX process. Wiz’s writeup is excellent and covers the technical nuances thoroughly, […]