Doing the Work: How to Architect a Systematic Security Program, Part 3
Building a security program from the ground up is a complicated, complex undertaking that can pay massive dividends down the road. We firmly believe that “the devil is in the details,” in that the more thought an organization invests in organizing their framework (see Part 1 of this series) and planning how to measure against […]
Web3 Trust Dependencies: A Closer Look at Development Frameworks & Tools
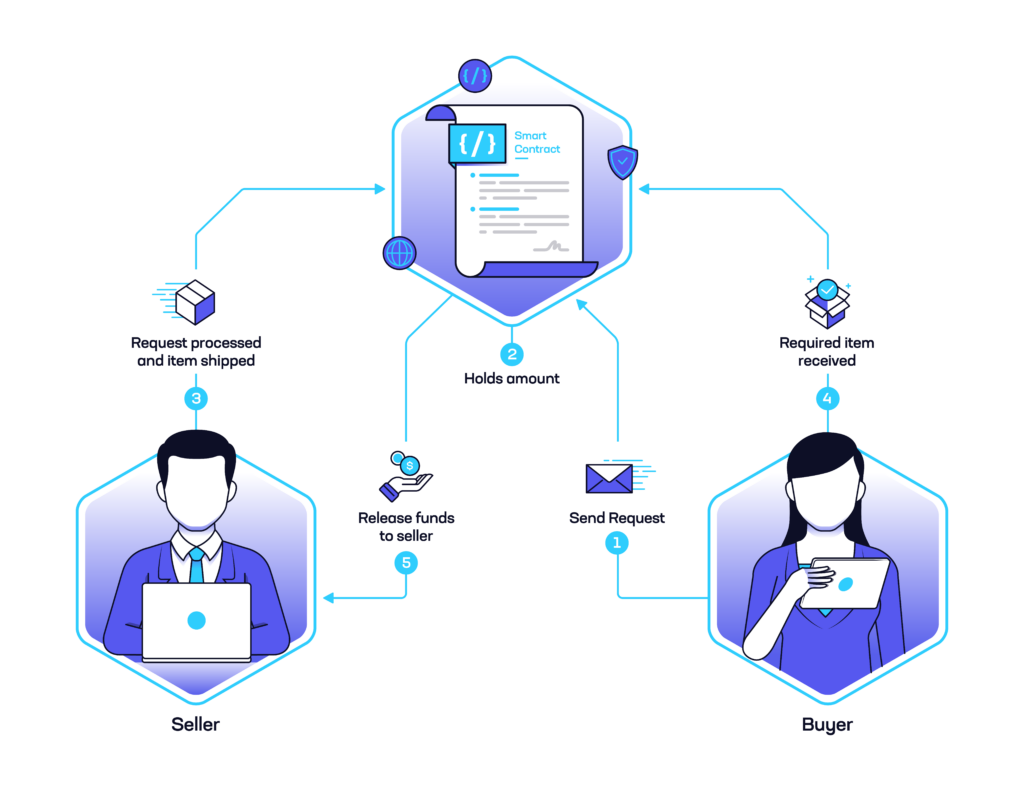
In the world of headline-grabbing smart contract exploits, developers and other stakeholders often skew their security attention in one direction; namely, they tend to focus on on-chain code, yet often neglect framework security. When writing smart contracts, this oversight can have significant negative security implications. Insecure frameworks or languages can subtly introduce vulnerabilities when compiling […]
Nosey Parker RegEx: A Positive Community Response
On December 7, 2022, Praetorian Labs released a regular expression-based (RegEx) version of our Nosey Parker secrets scanning tool (see press release). This version improves on two primary pain points the community has historically encountered with other secrets scanning tools. First, Nosey Parker RegEx offers the fastest secrets scanning capability on the market–100 gigabytes of […]
Instrumenting an Automotive Module for Bench Testing
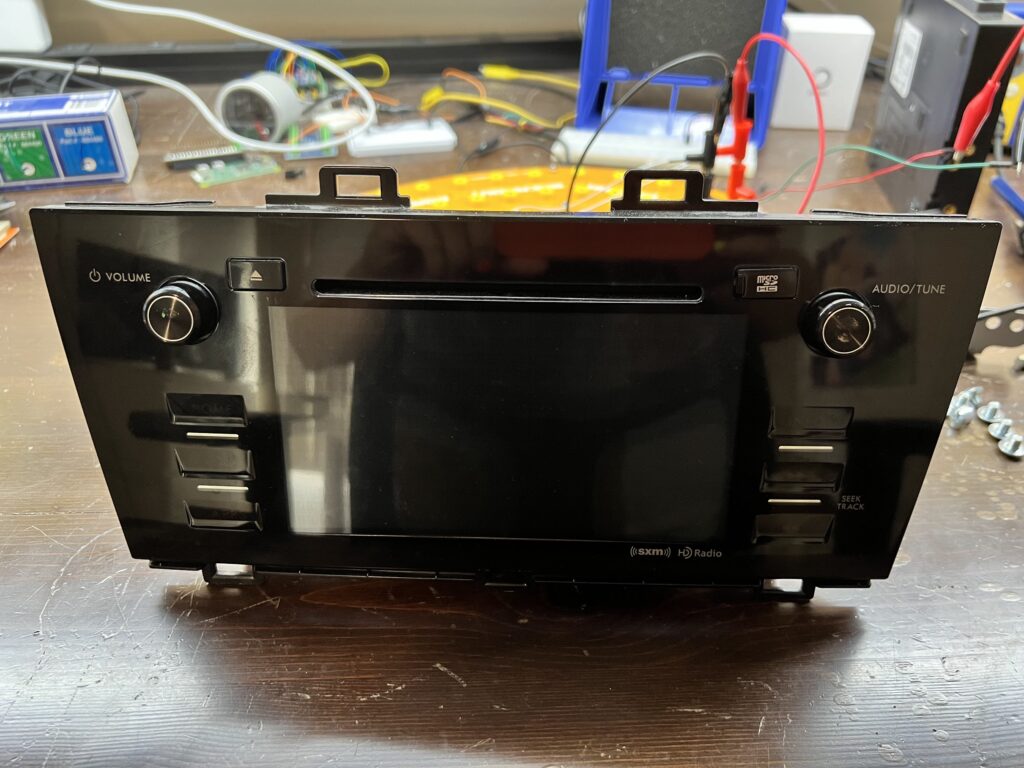
Finding vulnerabilities, hacks, exploits, and full root access are goals for security engineers when they begin to assess a device, right? But when working with hardware, you cannot simply dive into the hacking on day one. Your exploits will only be as successful as the setup work you’ve done! This post will discuss the process […]
Automating the Discovery of NTLM Authentication Endpoints

Recently, I have been working on adding support for automated enumeration and discovery of NTLM authentication endpoints to Chariot, our external attack surface and continuous automated red teaming product. Our red team requested this feature as a way to identify NTLM authentication endpoints exposed over HTTP that they could potentially leverage for password spraying attacks […]
Inspector, or: How I Learned to Stop Worrying and Love Testing in Prod
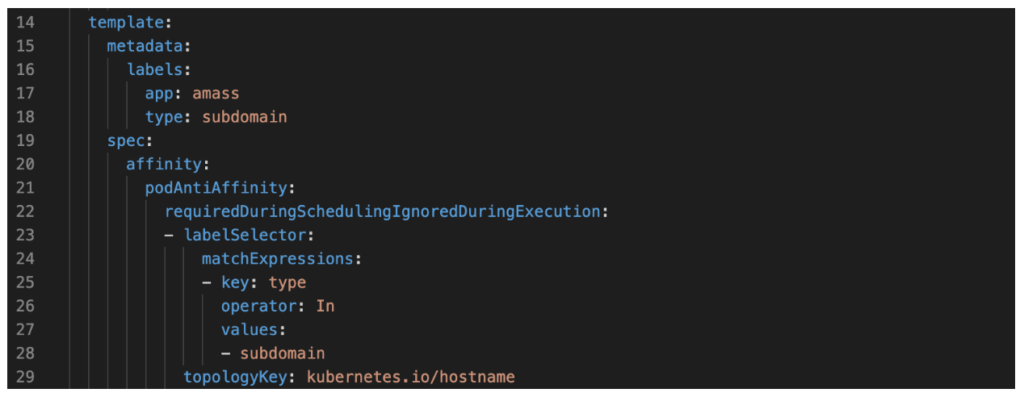
Overview Recently, I’ve shifted from primarily performing red team engagements to assisting in the development of Chariot, Praetorian’s attack surface management (ASM) and continuous automated red teaming (CART) product offering. Our Praetorian Labs team has developed multiple tools to support Chariot and our Services organization. One of these, a subsystem for the core asset enumeration […]
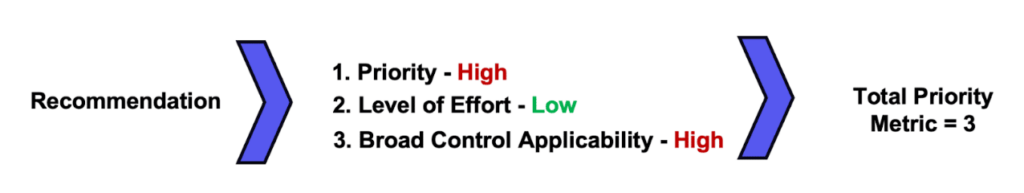
Measuring Up: How to Architect a Systematic Security Program – Part 2
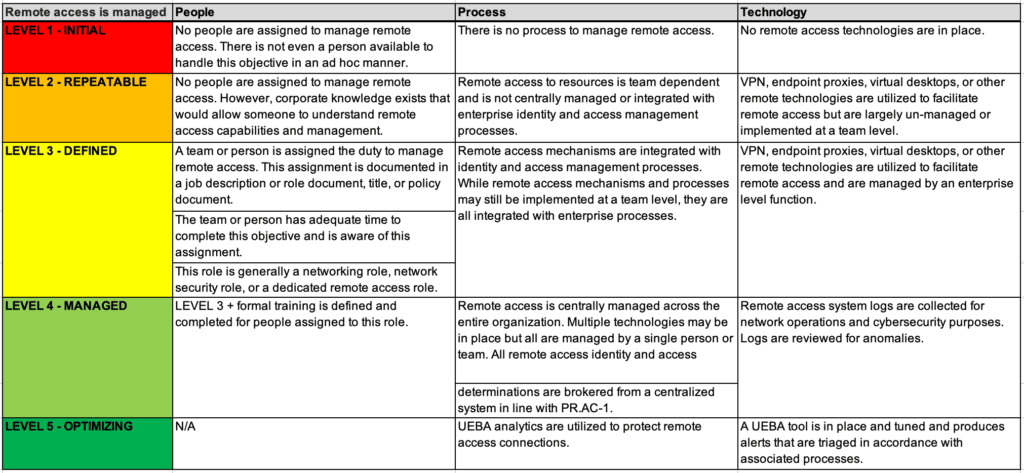
In Part 1 of this series , we discussed how organizations can go about selecting a framework for implementation. In order to effectively measure your organization against the selected framework, the organization must take five crucial steps before doing any assessment or analysis. Define the rating scale Define the rating criteria Determine how to address […]
From Self-Hosted GitHub Runner to Self-Hosted Backdoor
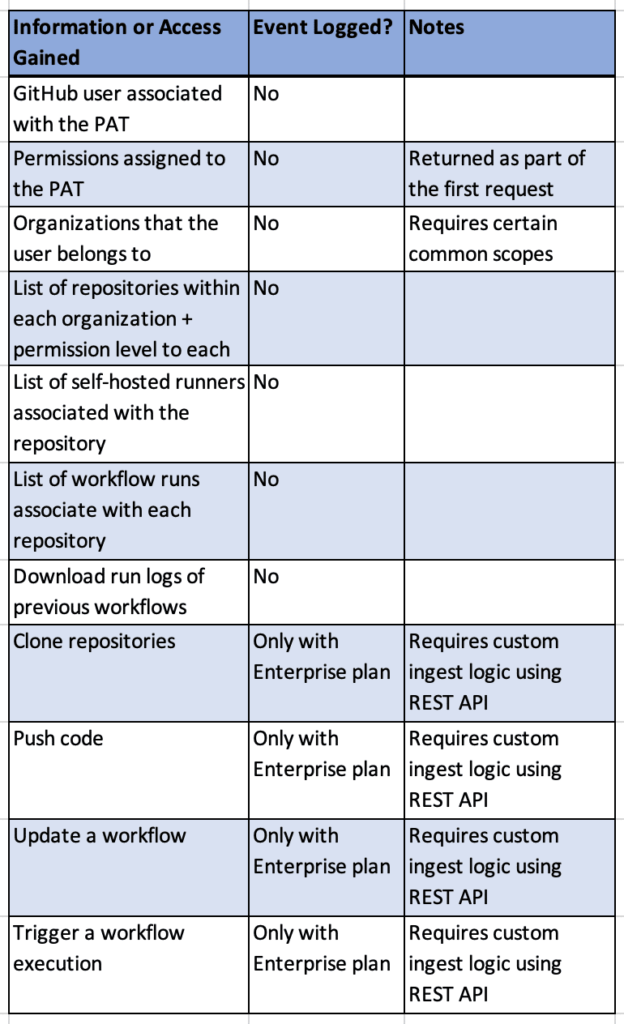
Overview Continuous Integration and Continuous Delivery (CI/CD) systems are powerful and configurable tools within modern environments. At Praetorian, we are seeing organizations migrate to SaaS solutions like GitHub (GitHub.com) as their source code management and CI/CD solution, instead of on-premises tools like BitBucket, Bamboo, and Jenkins. On our Red Team engagements , we routinely employ […]
Best Practices for Identity and Access Management When Using Google Cloud Platform
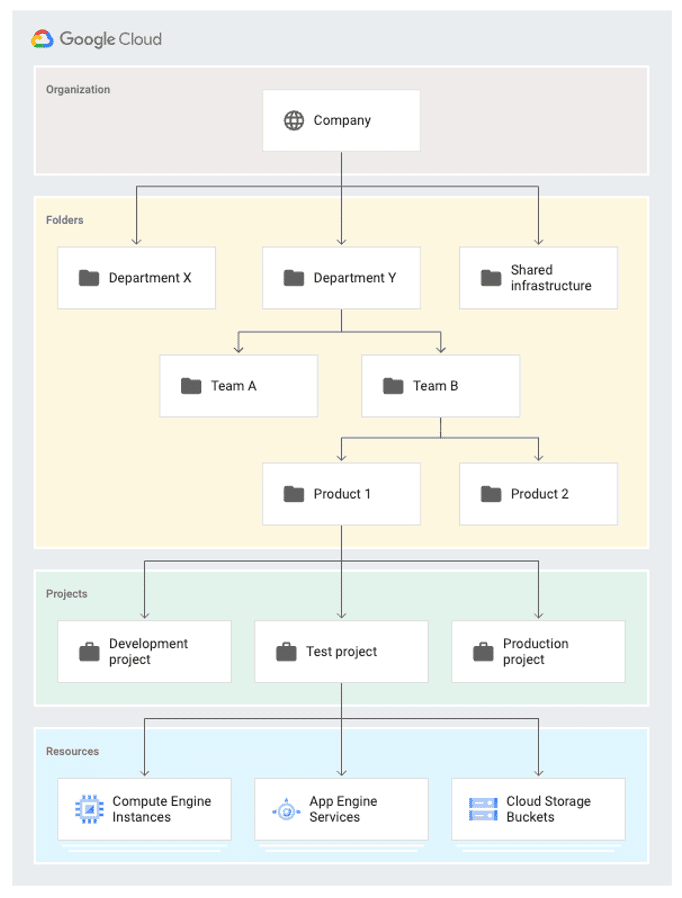
At Praetorian, one of our top priorities is looking over each client’s Identity and Access Management (IAM) structure. Several of our large clients use Google Cloud Platform (GCP), which is one of the top three cloud providers with about eight percent of the cloud services market share. During our work with GCP, we have noticed […]
Six Months of Finding Secrets with Nosey Parker
Earlier this year we announced Nosey Parker, a new scanner that uses machine learning techniques to detect hardcoded secrets in source code with few false positives. Since then we’ve continued its development and expanded its use in security engagements at Praetorian. In a few cases Nosey Parker has contributed to critical-severity findings, such as complete […]