The Vulnerability Time Gap
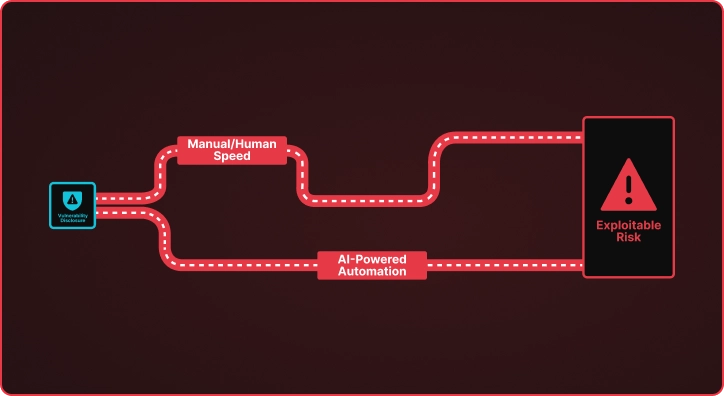
When CISA adds a new CVE to the Known Exploited Vulnerabilities catalog, a clock starts ticking. Security teams must understand the vulnerability, determine if they are exposed, and deploy detection mechanisms before adversaries weaponize the flaw. This process traditionally takes days or weeks of manual research by skilled security engineers who are already stretched thin.
The math is unfavorable. CISA’s KEV catalog has grown to over 1,200 entries, with new critical vulnerabilities added weekly. Meanwhile, the average time from vulnerability disclosure to active exploitation continues to shrink. Organizations face a fundamental question: how do you scale human expertise against an ever-expanding attack surface?
From Manual Research to Automated Intelligence
Praetorian’s CVE Researcher pipeline reimagines this challenge. Rather than replacing security engineers, the system amplifies their capabilities through AI-powered automation. The pipeline takes a CVE identifier as input and produces actionable outputs: comprehensive research reports, technology reconnaissance data, and validated detection templates ready for deployment.
The system operates through a coordinated sequence of specialized AI agents:
- Deep Research synthesizes information from vulnerability databases, security advisories, and technical references to build comprehensive understanding of each CVE.
- Technology Reconnaissance identifies affected products, vulnerable configurations, and detection indicators that map to real-world environments.
- Asset Correlation integrates with the Praetorian Guard platform to identify which organizational assets may be vulnerable, prioritizing response efforts.
- Detection Generation produces Nuclei templates through an iterative refinement process, validating each template for syntax correctness and detection accuracy.
- Exploitation Research analyzes each vulnerability from an offensive perspective, examining realistic attack vectors, exploitation techniques, and potential impact. This ensures detection templates target actual adversary behavior rather than theoretical indicators, and provides security teams with the context needed to prioritize remediation based on real-world risk.
The entire pipeline runs autonomously, transforming what previously required hours of security engineer time into minutes of automated processing. For critical vulnerabilities discovered overnight, security engineers arrive in the morning to find the research complete, detection templates validated, and review tickets waiting. Rather than spending their day on repetitive research tasks, they can apply their expertise where it matters most: validating findings, customizing detections for their specific environment, conducting deeper threat analysis, and focusing on proactive security initiatives that often get deprioritized when teams are overwhelmed by reactive work.
Measurable Impact
The CVE Researcher delivers quantifiable improvements across the vulnerability response lifecycle:
Speed: Research that traditionally consumed 4-8 hours of security engineer time completes in under 30 minutes. For high-volume vulnerability processing, this represents a 10x or greater efficiency gain.
Consistency: Every CVE receives the same thorough analysis. The system does not suffer from security engineer fatigue, varying expertise levels, or competing priorities.
Coverage: The pipeline processes vulnerabilities at scale, enabling organizations to maintain detection coverage across the full breadth of the CISA KEV catalog rather than triaging to a manageable subset.
Quality: Generated detection templates undergo automated validation before delivery, reducing the false positive burden on security operations teams.
Why This Matters for Security Leaders
The CVE Researcher represents a broader shift in how organizations can approach security operations. Rather than treating AI as a replacement for human expertise, the system demonstrates how AI can serve as a force multiplier, handling the volume and velocity challenges that overwhelm traditional approaches.
For CISOs evaluating their vulnerability management programs, several questions emerge:
- How quickly can your team develop detection capabilities for newly disclosed vulnerabilities?
- What percentage of CISA KEV entries do you have active detection coverage for?
- How do you prioritize security engineer time between reactive vulnerability research and proactive security improvements?
The CVE Researcher addresses these challenges by automating the research and template generation phases, freeing security teams to focus on remediation decisions and strategic initiatives.
Building a Proactive Defense Posture
Security programs increasingly require the ability to operate at machine speed while maintaining human judgment for critical decisions. The CVE Researcher embodies this hybrid approach: AI handles the research, correlation, and template generation while security teams retain control over deployment decisions and remediation priorities.
The system integrates with existing security workflows through the Praetorian Guard platform, enabling organizations to correlate vulnerability intelligence against their actual attack surface. This integration ensures that detection efforts focus on vulnerabilities that matter to each specific environment rather than generic severity scores.
Next Steps
Vulnerability management continues to evolve from periodic scanning toward continuous, intelligence-driven operations. Organizations that leverage AI to accelerate their response capabilities will maintain defensive advantages as the threat landscape continues to accelerate.
If your organization struggles to keep pace with emerging vulnerabilities or wants to explore how AI can enhance your security operations, contact Praetorian to discuss how the CVE Researcher pipeline can integrate with your vulnerability management program.
Frequently Asked Questions
What is the CVE Researcher?
Praetorian’s CVE Researcher is an AI-powered pipeline that automates vulnerability analysis. It takes a CVE identifier as input and produces comprehensive research reports, technology reconnaissance data, and validated Nuclei detection templates ready for deployment.
How fast does the CVE Researcher process a new vulnerability?
Research that traditionally takes 4-8 hours of security engineer time completes in under 30 minutes, representing a 10x or greater efficiency gain for vulnerability response.
Does the CVE Researcher replace security engineers?
No. The system is designed as a force multiplier that handles volume and velocity challenges. Security engineers retain control over deployment decisions, remediation priorities, and strategic judgment calls.
How does the CVE Researcher integrate with existing security workflows?
The pipeline integrates with the Praetorian Guard platform to correlate vulnerability intelligence against an organization’s actual attack surface, ensuring detection efforts focus on vulnerabilities relevant to each specific environment.