Rogue IT Identification
Enable your business without sacrificing security. Proactively identify and mitigate rogue IT that could compromise your business
Keep Track of Your Digital Footprint in Real-Time
Identify Your Shadow IT
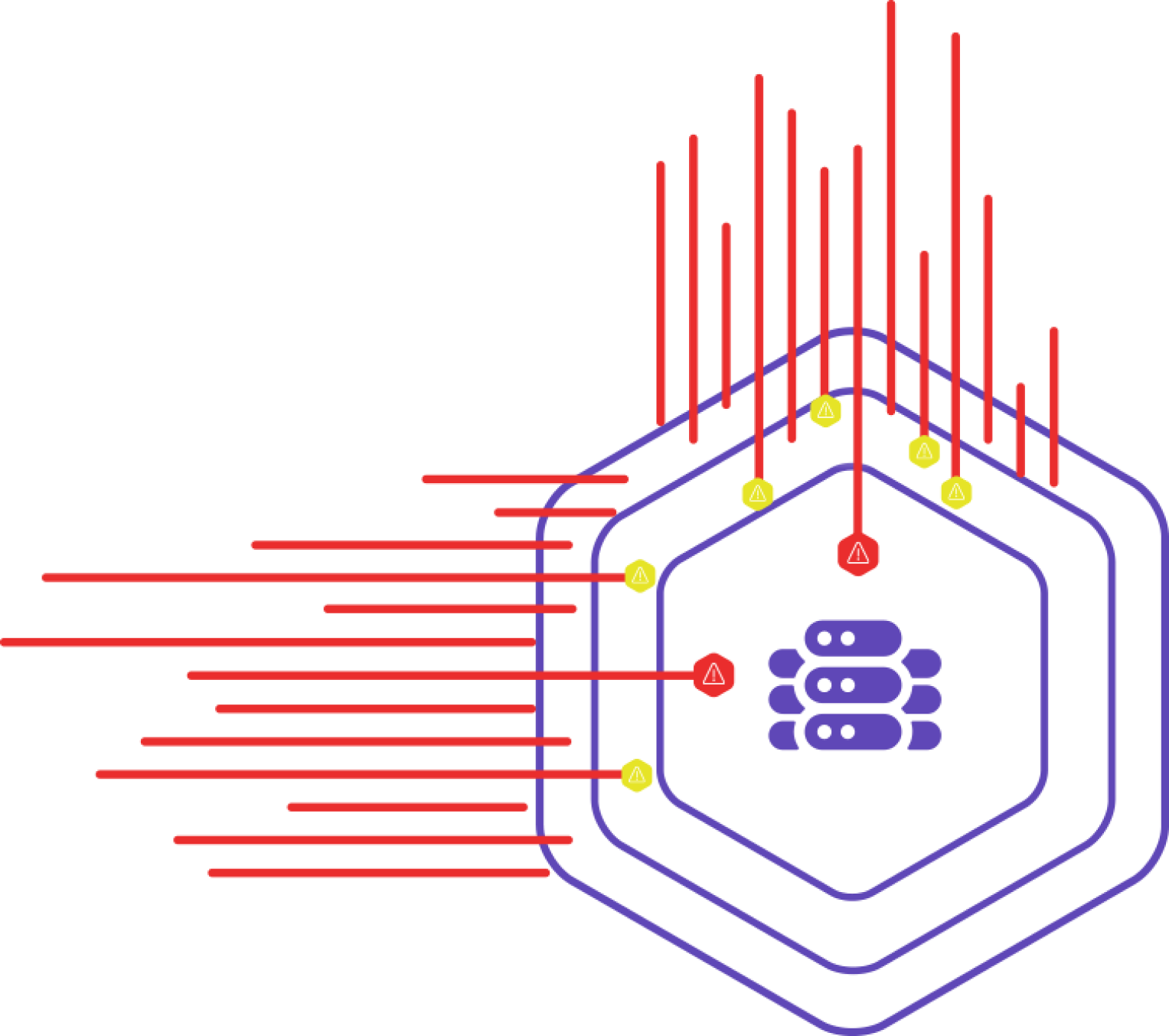
Identify and Mitigate Unknown Attack Surfaces
Simplify attack surface management with a team of adversarial experts who aim to streamline your business operations while helping you secure your environment
Map Internet Footprint
Understand and visualize your full attack surface through our continuous offensive security platform, Chariot, which crawls your business assets in real time
Inventory Core Infrastructure
Leverage core infrastructure integrations to form a complete picture and contextualize relationships between assets
Alert in Real-Time
Perform just-in-time cloud scanning to stay in aligned with your business units while keeping them informed of the risks in real-time
Ready to Discuss Your Rogue IT Identification Initiative?
Praetorian’s Offense Security Experts are Ready to Answer Your Questions