Offensive Security
Continuous Penetration Testing
Continuously test your cybersecurity program against real‑world attacks with Praetorian’s AI‑enabled penetration testing.
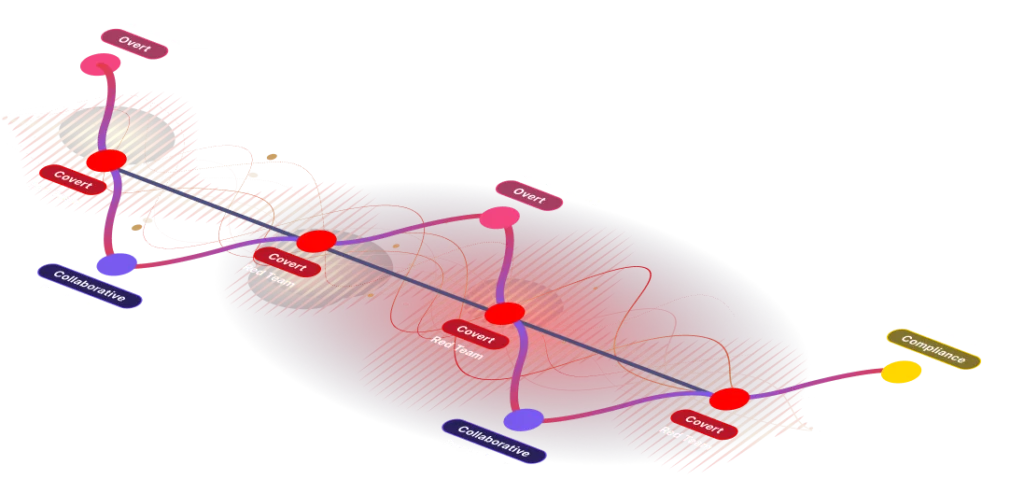
The Sine Wave of AI Enabled Continuous Penetration Testing
The Sine Wave of Continuous Penetration Testing describes how real-world security resilience is built: a repeating cycle of overt penetration testing (broad, visible assessments), collaborative purple teaming (cross-team detection + improvement), and covert red teaming (targeted, stealthy attack emulation). By oscillating through these modes continuously, organizations surface new weaknesses, validate controls, and embed security practices into development and operations — shortening time-to-remediation and shrinking an attacker’s window of opportunity.
Overt Pentesting (Breadth)
Scheduled, high-coverage tests and automated scans that map the attack surface and catch obvious vulnerabilities.
Purple Teaming (Collaboration)
Structured, collaborative exercises where offensive and defensive teams work together to tune detection, telemetry, and playbooks.
Covert Red Teaming (Depth):
Stealthy, goal-oriented emulations that chain low-severity issues into high-impact attack paths and test real-world detection and response. Moving continuously through these modes ensures issues are found as they appear, fixes are validated, and defenders are trained — converting sporadic audits into an ongoing program of risk reduction and resilience.
Real-World Threat Emulation
Stay ahead of the attacker through simulated attacks using the latest tactics, techniques, and procedures (TTPs) customized to . With a goal of each engagement of gaining unauthorizes access into your environment, our team of experts provide unparalleled insight into your organizations security controls, policies, and procedures and their ability to withstand an actual attack.
Expert Insight
Praetorians team of offensive security engineers bring years of experience and expertise to the table, working closely with your organization to understand its unique challenges and devise customized solutions that meet your specific security goals.
Test Your Cybersecurity Program’s Resilience Over Time
Customized Attack Simulations
Tailored scenarios that reflect your unique business risks and threat profile, ensuring relevance and maximum impact on your security readiness
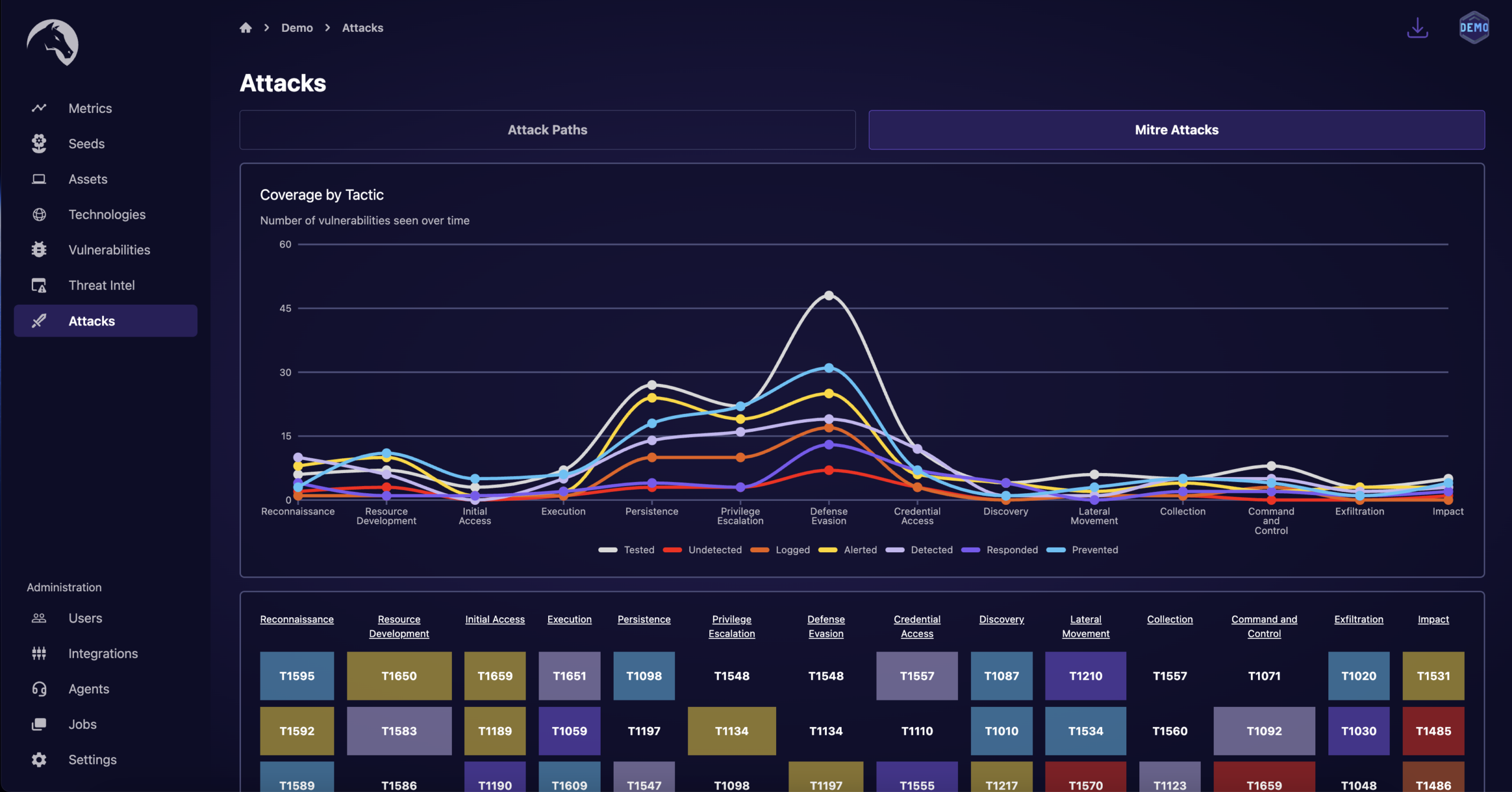
Advanced Reporting and Analytics
Detailed insights and actionable intelligence provided through comprehensive reports, enabling informed decision-making and strategic security planning.
Integrated Threat Intelligence
Incorporation of the latest threat intelligence from Praetorian Labs to inform red team operations, ensuring that your defenses are tested against current and emerging threats.
Dedicated Support and Collaboration
A dedicated team of customer obsessed experts works alongside your in-house security staff, fostering a collaborative environment for knowledge sharing and skill development.
Boost Your Prevention, Detection, and Response Capabilities
Enhanced Security Posture
By continuously challenging your systems, you can proactively identify and remediate vulnerabilities, leading to a stronger, more resilient security posture.
Reduced Risk of Breaches
Regular and rigorous testing reduces the likelihood of successful cyber-attacks, protecting your organization from potential financial and reputational damage.
Compliance and Assurance
Demonstrate to regulators, customers, and partners that your cybersecurity efforts are thorough and effective, aligning with industry best practices and compliance requirements.
Strategic Security Investments
Make informed decisions about where to allocate your security budget, focusing on areas of greatest need and potential impact, as revealed by red team findings.
Frequently Asked Questions
How does continuous penetration differ from traditional security assessments?
Continuous penetration testing goes beyond point-in-time assessments, providing ongoing evaluations and simulations to uncover vulnerabilities that may arise after initial assessments.
Who can benefit from Praetorian's continuous penetration testing service?
Our service is ideal for enterprises aiming to strengthen their cybersecurity defenses to protect sensitive data.
How do customized attack simulation scenarios add value?
By simulating real-world attacks specific to your organization, Praetorian’s customized scenarios uncover vulnerabilities that generic assessments often miss. This allows for targeted improvements and greater preparedness against tailored cyber threats.
What role does actionable intelligence play in our security strategies?
Actionable intelligence insights provide you with dynamic, up-to-date knowledge about threats and vulnerabilities within your systems. This empowers informed decision-making, efficient resource allocation, and the ability to stay one step ahead of potential threats.
How does having a dedicated team of experts benefit our organization?
With a dedicated team of cybersecurity experts, you gain access to ongoing guidance, personalized recommendations, and a deep understanding of your organization’s unique challenges. This ensures that your security strategies are tailored to your specific needs and goals.
Can Praetorian's continuous penetration testing service assist with compliance requirements?
Yes, our service helps align your security practices with industry standards and regulatory requirements, offering compliance and assurance while simultaneously enhancing your overall security posture.
How does continuous penetration testing contribute to reducing the risk of breaches?
By continuously assessing and strengthening your defense mechanisms, continuous red teaming helps identify and mitigate vulnerabilities before they can be exploited by malicious actors. This proactive approach significantly reduces the risk of breaches.
How can we get started with Praetorian's continuous red teaming service?
You can get started by contacting our team and scheduling a consultation. Our experts will assess your organization’s unique needs and guide you through the process of leveraging continuous red teaming for enhanced security.
Ready to Discuss Your
Continuous Penetration Testing Initiative?
Praetorian’s Offense Security Experts are Ready to Answer Your Questions