A simple and effective way to detect Broadcast Name Resolution Poisoning (BNRP)
A natural question that arises after an organization experiences a BNRP attack is “How can this be prevented?” The answer is simple on paper. To completely mitigate the risk, legacy Broadcast Name Resolution protocols should be disabled by policy. This is easier said than done, especially on large networks where the necessary data flows of […]
NIST Cybersecurity Framework Vignettes: Broadcast Name Resolution Poisoning
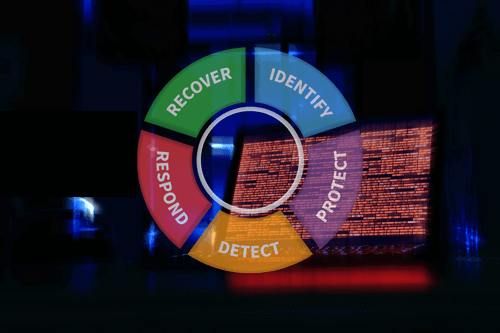
Our NIST Cybersecurity Framework Vignettes series focuses on the best applications of NIST CSF for your organization. This article addresses the tactic of Broadcast Name Resolution Poisoning.
Threat Hunting: How to Detect PsExec
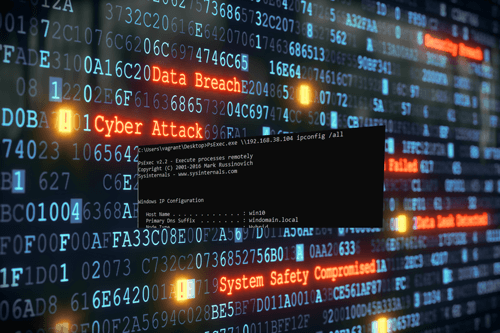
This article profiles the use of the PsExec command-line tool as a cyber-attack technique, and how threat hunters can detect it.
NIST Cybersecurity Framework Vignettes: Phishing
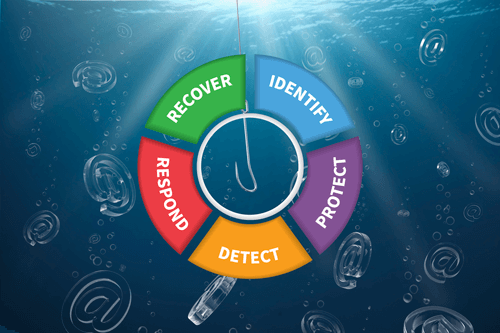
This article examines the application of the NIST Cybersecurity Framework for addressing phishing concerns.
Active Directory Computer Account SMB Relaying Attack

This article outlines a unique Active Directory attack vector that arises when a computer account has administrative access to another computer.
10 Cybersecurity Technical Priorities for Telework
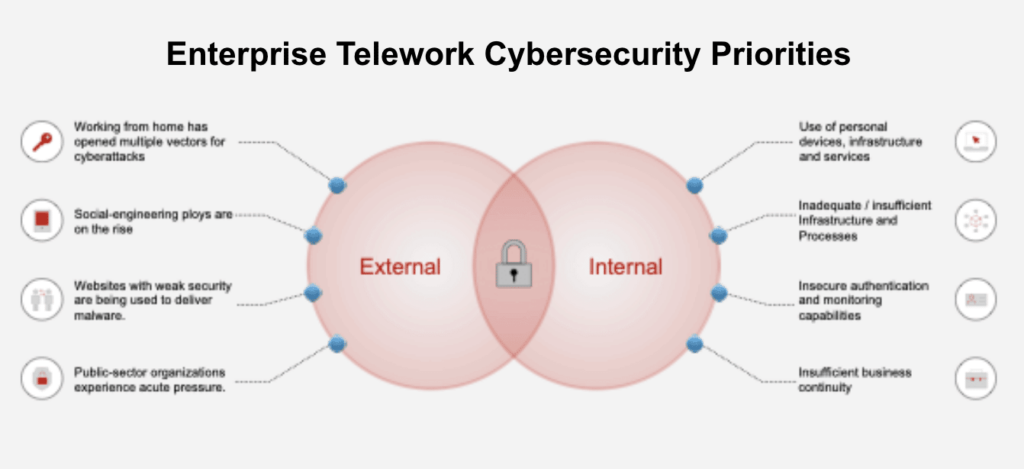
As Telework becomes a new normal, cybersecurity professionals must consider the greater attack surface. This article suggests the top focus areas for consideration.
Extending LLVM for Code Obfuscation (2 of 2)
In part one, we covered setting up a development environment for working with LLVM and developed a simple pass that inserted junk code into binaries during compilation to hinder signature-based detection and manual reverse engineering efforts. In this article, we develop a more complex pass that automatically encrypts string literals during the compilation process by […]
Extending LLVM for Code Obfuscation (1 of 2)

Part one of this article covers the necessary background on LLVM, setting up a development environment, and developing an LLVM pass for junk code insertion in an attempt to generate unique polymorphic binaries.
Lessons from ATT&CKcon 2.0 and SANS Purple Team Summit
In this post, I’ll be going over how I draw value from conferences and the lessons learned, as well as planned projects Praetorian has going into the end of 2019 and start of 2020.
Bypassing Google’s Santa Application Whitelisting on macOS (Part 2 of 2)
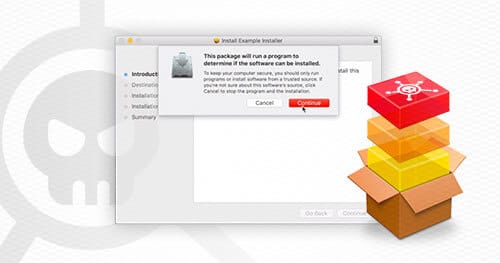
This article will examine an example flat PKG installer and demonstrate how to technically abuse Google’s Santa application whitelisting.