Nerva is a high-performance, open-source CLI tool that identifies what services are running on open network ports. It fingerprints 120+ protocols across TCP, UDP, and SCTP, averaging 4x faster than nmap -sV with 99% detection accuracy. Written in Go as a single binary, Nerva helps security teams rapidly move from port discovery to service identification.
In 2022, our intern class built fingerprintx for service fingerprinting. We’ve continued developing it ever since. Today we’re releasing Nerva, a high-performance CLI tool that identifies 120+ protocols across TCP, UDP, and SCTP. Migrating to a new project was a tough decision, but it allowed us to overhaul the priority queuing system and expand protocol coverage by 2.5x. Nerva now scans 120+ services in under 3 minutes with 99% detection accuracy, averaging 4x faster than nmap -sV. Written in Go as a single binary, Nerva helps security teams rapidly identify what’s running on discovered ports.
The Gap Between Discovery and Understanding
You’ve just finished a port scan against a target network and have identified thousands of open ports across the client’s infrastructure. Port 8080 is open on dozens of hosts. Port 9200 appears on a handful of servers. Something is listening on port 4840.
Now comes the question every pentester wonders: what’s actually running on these ports?
Port 8080 could be a development server someone forgot to decommission, a Jenkins instance with default credentials, or a Kubernetes API server that shouldn’t be exposed. The port number alone doesn’t give you all the answers. Identifying the service behind it could be the difference between a routine finding and a critical one.
This is where the reconnaissance pipeline has a gap. We have excellent tools for finding open ports. Masscan can scan the entire internet in minutes using its custom TCP/IP stack. RustScan discovers 65,000 ports in seconds. Naabu handles large target lists with clean, pipeable output. Port discovery is essentially a solved problem.
But discovering that a port is open and understanding what’s running on it are different challenges. Nmap can perform comprehensive service detection, but it is optimized for accuracy over speed. When you’re dealing with thousands of endpoints discovered by a fast scanner, waiting for Nmap to probe each one creates a bottleneck. Tools like zgrab2 are fast but require specifying the protocol ahead of time, which assumes you already know what you’re looking for.
At Praetorian, we kept hitting this friction point across penetration tests. We had great tools for finding open ports, but nothing purpose-built for the next step, which is quickly identifying what services those ports were running.
So we built Nerva.
Where Nerva Fits in Your Toolkit
The modern reconnaissance pipeline has distinct stages. Understanding where each tool excels helps you build an effective workflow.
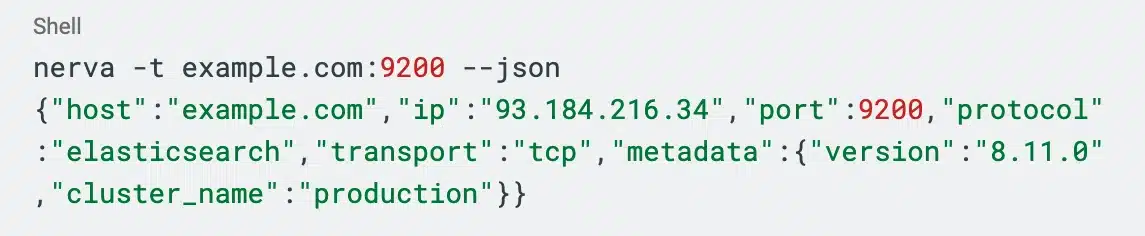
Nerva focuses entirely on the fingerprinting problem. You provide a host and port that you already know is open, and it identifies what’s running:
This separation of concerns means you can pair Nerva with whatever discovery tool fits your workflow:
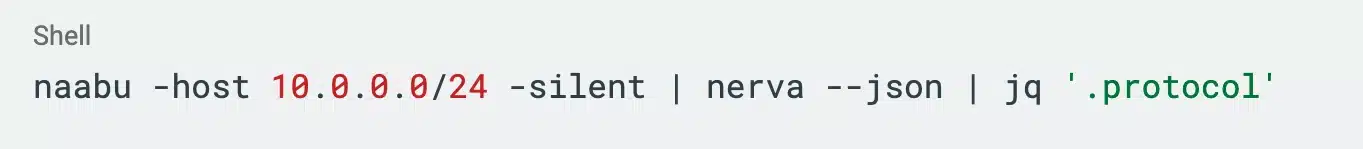
Each tool does what it’s best at, and the pipeline moves from broad discovery to focused investigation.
What Nerva Recognizes
Nerva identifies over 120 protocols, with particular depth in areas that security tools often overlook.
Common services are well-covered: SSH, HTTP/HTTPS, MySQL, PostgreSQL, MongoDB, Redis, RDP, and dozens more. For web services, Nerva includes technology detection via Wappalyzer fingerprints to identify specific platforms and frameworks. But we’ve also invested in protocols that matter for security assessments yet rarely get attention from general-purpose tools.
Industrial control systems represent one such area. When assessing an operational technology network, quickly identifying which devices speak which protocols provides immediate visibility into the control system landscape, often revealing devices that weren’t properly documented or shouldn’t be network-accessible.
Telecom protocols are another focus. When assessing mobile core networks, quickly identifying Diameter nodes, SS7 gateways, and signaling infrastructure reveals the authentication and routing topology, often exposing interfaces that carriers assume are internal but aren’t properly segmented.
Modern infrastructure gets attention too. Vector databases like ChromaDB and Pinecone are increasingly common in AI-powered applications. Message brokers like Kafka, NATS, and Pulsar handle event streaming. Container orchestration exposes Kubernetes API servers. Each protocol plugin extracts relevant metadata, version numbers, configuration details, cluster names.
Smart Detection
When you point Nerva at port 22, it doesn’t cycle through all 120+ protocol plugins hoping one matches. It knows port 22 is almost certainly SSH, so it tries that first. If SSH doesn’t match, it falls back to other possibilities, but the fast path handles common cases in a single probe.
This port-aware prioritization makes a meaningful difference at scale. In our benchmarks, Nerva scans 100 services in under 3 minutes with 99% detection accuracy, which is 4x faster than nmap (-sV) on average. When fingerprinting tens of thousands of services, that difference compounds quickly. Nerva tries to be smart about what it checks first while remaining thorough enough to catch services on non-standard ports.
For large-scale scanning, Nerva also offers a fast mode (–fast) that only checks the default port for each protocol, serving as an optimization when you need speed over completeness.
Beyond TCP
Most fingerprinting tools assume TCP. But some of the most interesting targets from a security perspective use other transports.
UDP services include DNS servers, SNMP agents, NTP services, DHCP, and various VPN protocols. Industrial control systems often use UDP for time-sensitive communications. Nerva handles UDP fingerprinting natively.
SCTP is the transport protocol that telecom core networks rely on. Diameter, which handles authentication in LTE and 5G networks, runs over SCTP. So does SS7-over-IP for legacy circuit-switched interworking. On Linux systems, Nerva can fingerprint these services where TCP-only tools are blind.
Working with Results
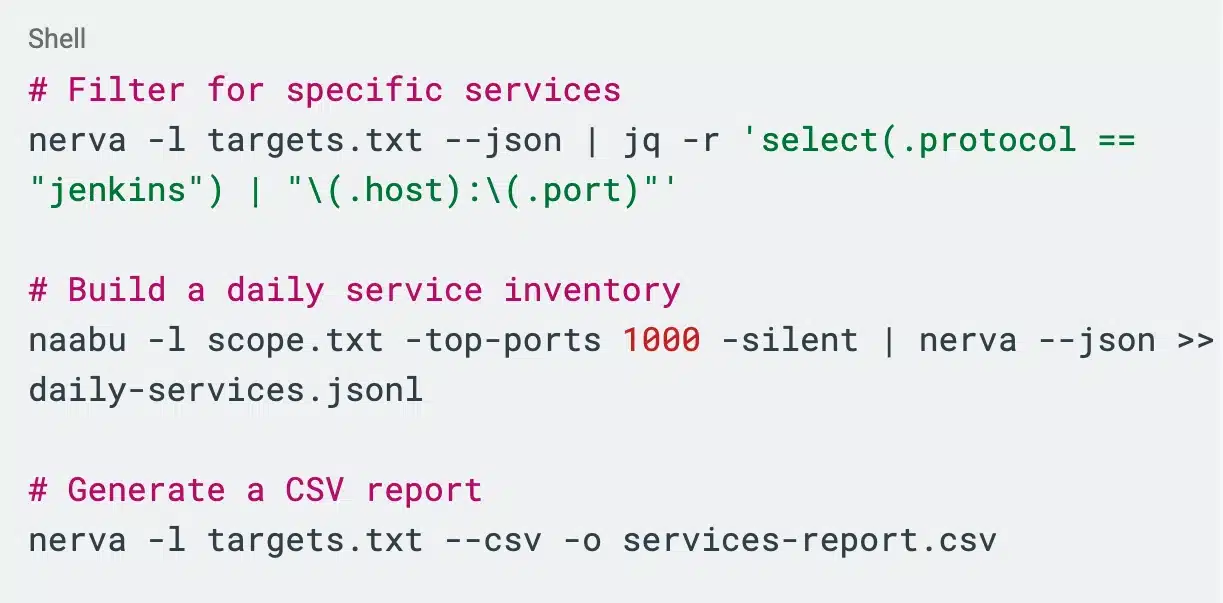
We designed Nerva to slot into existing security workflows rather than demanding you change how you work. Nerva’s JSON output streams to stdout by default, chaining naturally with jq, databases, or custom scripts. You can switch to CSV when the results need to land in a spreadsheet. Plain text is available when you just want to see what’s running.
For teams building custom tooling, Nerva is available as a Go library. The scan and plugins packages expose the same detection logic as the CLI, letting you embed fingerprinting directly into automated pipelines, custom scanners, or internal security tools.
Part of a Larger Toolkit
Nerva fits into Praetorian’s open-source security ecosystem alongside Brutus, Titus, and Constantine. Each tool handles a distinct phase of security work, and they chain naturally together.
Nerva provides the foundation: identifying what services are running across your targets. That inventory feeds directly into what comes next. Brutus tests credentials against the services that Nerva discovers. Titus scans for exposed secrets in code, configurations, and HTTP traffic. Constantine goes deeper, autonomously analyzing source code repositories for vulnerabilities and generating patches, turning static analysis into actionable fixes. Findings flow between tools cleanly, letting you build assessment pipelines where each stage hands off to the next.
Real-World Applications
Nerva fits wherever service identification matters. During penetration tests, it slots in right after port discovery. For larger-scale work, it pairs naturally with fast scanners like Naabu or Masscan to maintain asset inventories across entire networks. The same approach works in CI/CD pipelines, where Nerva can verify that only expected services are exposed after deployment, catching misconfigurations before they reach production.
Bug bounty hunters can use it to quickly triage scope targets, prioritizing where to dig deeper based on what’s actually running. In operational technology environments, ICS protocol support reveals the control system topology — including Modbus, S7comm, and BACnet services — that might not be documented or shouldn’t be network-accessible at all. Telecom engagements benefit from SCTP support, making Diameter nodes and signaling infrastructure visible where TCP-only tools see nothing.
Get Started with Nerva
Nerva is available now at https://github.com/praetorian-inc/nerva. Prebuilt binaries for Linux, macOS, and Windows are on the releases page: https://github.com/praetorian-inc/nerva/releases.
If you find bugs, want to contribute protocol plugins, or have feature requests, open an issue. We’re actively developing Nerva and want to hear how you’re using it.
Frequently Asked Questions
What is Nerva?
Nerva is a free, open-source command-line tool that identifies what network services are running on open ports. It fingerprints 120+ protocols across TCP, UDP, and SCTP transports, written in Go as a single binary with no external dependencies.
How does Nerva compare to nmap service detection?
Nerva averages 4x faster than nmap -sV with 99% detection accuracy. Nmap is optimized for accuracy over speed; Nerva uses port-aware priority queuing to try the most likely protocols first, making it significantly faster when scanning thousands of endpoints.
What protocols does Nerva support?
Nerva supports 120+ protocols including common services (SSH, HTTP, MySQL, PostgreSQL, Redis, RDP), industrial control systems (Modbus, S7comm, BACnet, OPC-UA), telecom protocols (Diameter, SS7-over-IP via SCTP), modern infrastructure (Kubernetes API, Kafka, NATS, ChromaDB), and more.
How do I install Nerva?
Download a prebuilt binary for Linux, macOS, or Windows from the GitHub releases page, or build from source with Go. Nerva ships as a single binary with no external dependencies.
Can I use Nerva as a Go library?
Yes. The scan and plugins packages expose the same detection logic as the CLI, letting you embed service fingerprinting directly into custom tools, automated pipelines, or internal security scanners.
How does Nerva handle non-standard ports?
Nerva uses port-aware priority queuing to try the most likely protocols first based on port number, but falls back to checking all applicable protocols if the expected service doesn’t match. The –fast flag limits checks to default ports only when speed is the priority.