Running a .NET Assembly in Memory with Meterpreter

In this blog post I will discuss leveraging Meterpreter’s powershell module to execute .NET assemblies in-memory. Metasploit and Meterpreter are effective and useful tools, but occasionally one encounters a situation where they lack features. Cobalt Strike (a different Command and Control framework) contains an execute-assembly command providing in-memory .NET execution for situations where it lacks built in commands. Meterpreter contains the features required to perform the same behavior, albeit slightly less polished.
Active Directory Visualization for Blue Teams and Threat Hunters

As a network defender, it can be easy to attribute a certain degree of omnipotence to attackers. Advanced threats have an uncanny knack for figuring out how to move through an environment without regards for passwords, roles, permissions, or what “should” be possible.
Signed Binaries Proxy Execution – T1218
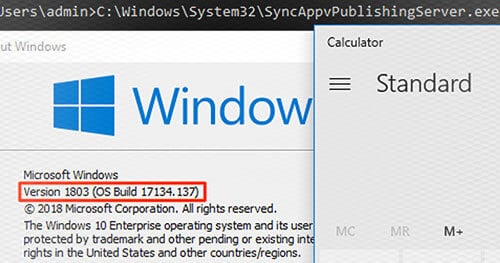
The MITRE ATTACK April release included is a new TTP known as ‘Signed Binaries Proxy Execution’ which is T1218. This TTP is based on an attacker using signed binaries to perform malicious activities.
Signed Scripts Proxy Execution – T1216
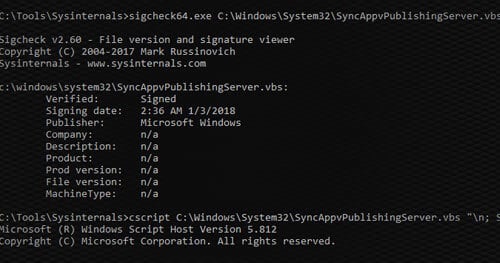
Many organizations trust all signed code from Microsoft. Unfortunately, there are many ways in which attackers can use this trust against them. Previously, we covered using signed binaries to perform malicious activities. In this post, we will be covering how to use signed scripts.
How to use Kerberoasting – T1208 for Privilege Escalation
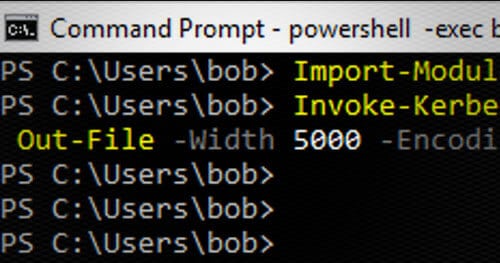
In our experience, Kerberoasting is an attack that is similar to others in that defenders need to fully under it to be able to properly migrate the risks. It’s our goal that through pushing this content into the MITRE ATT&CK framework we have increased the awareness of this TTP so that organizations can be better protected in the future.
Privilege Escalation in AWS with PassRole Attacks
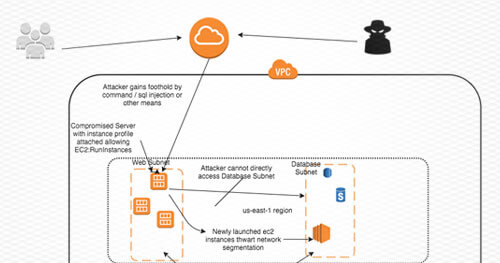
All instances launched by AWS by default have instance credentials supplied by the AWS metadata service. AWS operators can attach PassRole policies given to an instance at launch time.
Breaking Through Single Sign On (SSO)
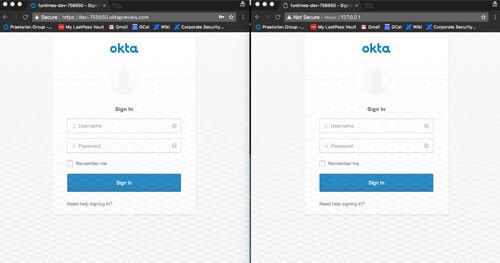
During my internship with Praetorian, I was able to create a new tool—Okta Watering Hole—that was used on some of the red team engagements. I created this tool because our team ran into the issue of not being able to get past two factor authentication on various web portals—so this is how we got around that. Okta Watering Hole sets up a carbon copy of a target Okta site and begins to capture credentials and sessions of visitors. This can be used to check how a company’s procedures and policies stand up to the “next generation” phishing attacks we are beginning to see. This new tool supports traditional phishing attacks as well as targeting two factor authentication devices—meaning perimeter security has to work double time.
Path.Combine Security Issues in ASP.NET Applications
Path traversal vulnerabilities are a common class of web application vulnerability, where an attacker aims to access files outside of the intended directory by using “../” patterns to traverse directories or by using absolute paths. These vulnerabilities are commonly found in file upload or download functionality of an application.
How to Mitigate Mimikatz WDigest Cleartext Credential Theft

Penetration testers and malicious adversaries often focus on using the easiest attack vector to achieve their objectives. One common attack vector that has been around for several years is to use a tool called Mimikatz and steal cleartext credentials from memory of compromised Windows systems.
Reversing and Exploiting Embedded Devices: The Software Stack (Part 1)
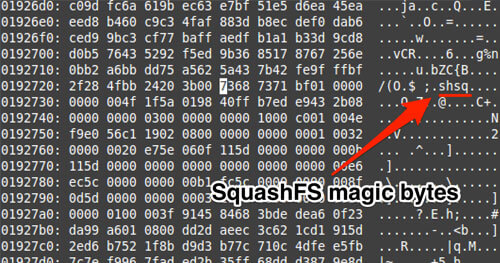
Over the course of the past few months I’ve been traveling around educating people on exploiting embedded devices. My slides alone aren’t able to provide enough information, so I wanted to write everything out for people to digest online. The following blog post is “Part 1”, which will introduce the reader to the software side of embedded devices. I decided to cover software first since most flaws reside within the software stack, ranging from binary applications to drivers. Part 2 will cover the Hardware stack with a focus on educating the reader on how JTAG actually works and how to leverage Hardware modifications to either bypass password protections or to extract secrets that may be baked into the targeted devices.