Phantom of the Pipeline: Abusing Self-Hosted CI/CD Runners
Introduction Throughout numerous Red Teams in 2022, a common theme of Source Control Supply Chain attacks in GitHub repositories has emerged. After many hours manually hunting for and exploiting these attack paths, we’ve built an all-in-one toolkit called Gato (Github Attack Toolkit) for finding and attacking repositories where these misconfigurations are present. We released the […]
Nosey Parker RegEx: A Positive Community Response
On December 7, 2022, Praetorian Labs released a regular expression-based (RegEx) version of our Nosey Parker secrets scanning tool (see press release). This version improves on two primary pain points the community has historically encountered with other secrets scanning tools. First, Nosey Parker RegEx offers the fastest secrets scanning capability on the market–100 gigabytes of […]
Instrumenting an Automotive Module for Bench Testing
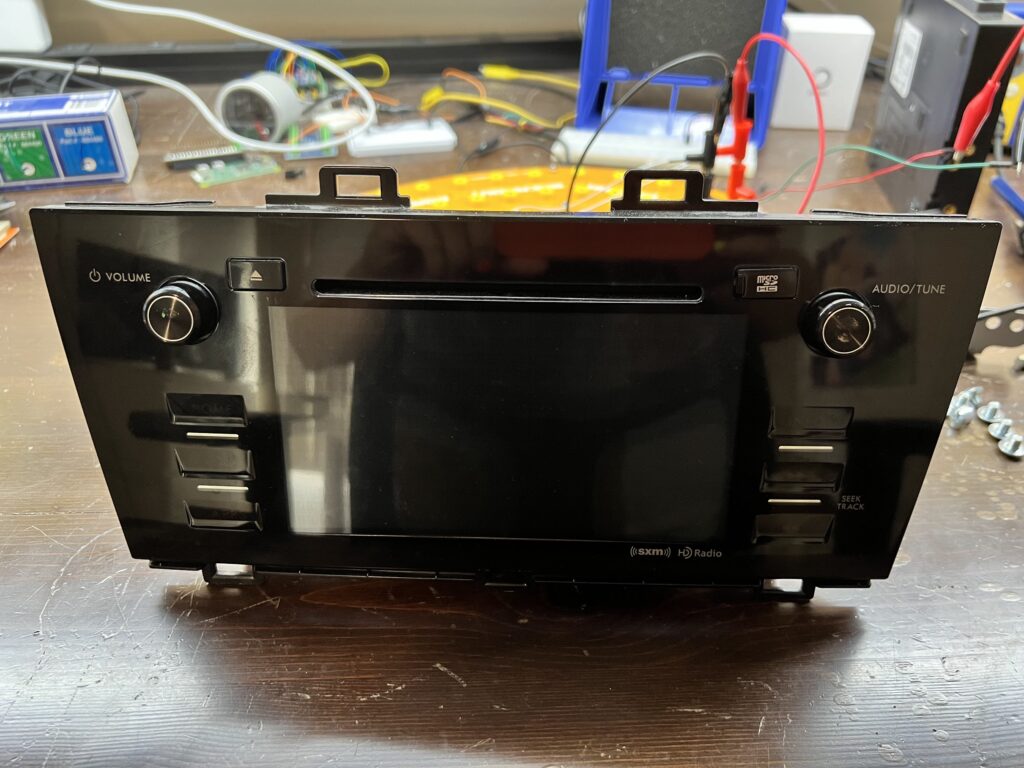
Finding vulnerabilities, hacks, exploits, and full root access are goals for security engineers when they begin to assess a device, right? But when working with hardware, you cannot simply dive into the hacking on day one. Your exploits will only be as successful as the setup work you’ve done! This post will discuss the process […]
Automating the Discovery of NTLM Authentication Endpoints

Recently, I have been working on adding support for automated enumeration and discovery of NTLM authentication endpoints to Chariot, our external attack surface and continuous automated red teaming product. Our red team requested this feature as a way to identify NTLM authentication endpoints exposed over HTTP that they could potentially leverage for password spraying attacks […]
Inspector, or: How I Learned to Stop Worrying and Love Testing in Prod
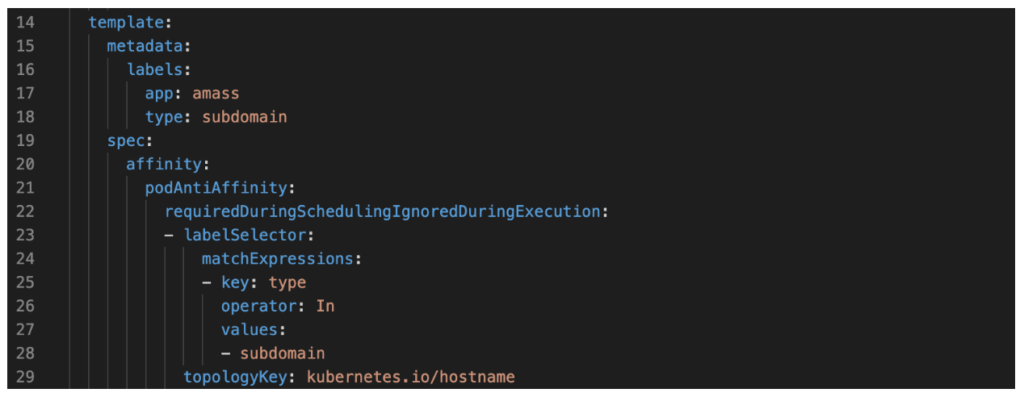
Overview Recently, I’ve shifted from primarily performing red team engagements to assisting in the development of Chariot, Praetorian’s attack surface management (ASM) and continuous automated red teaming (CART) product offering. Our Praetorian Labs team has developed multiple tools to support Chariot and our Services organization. One of these, a subsystem for the core asset enumeration […]
From Self-Hosted GitHub Runner to Self-Hosted Backdoor
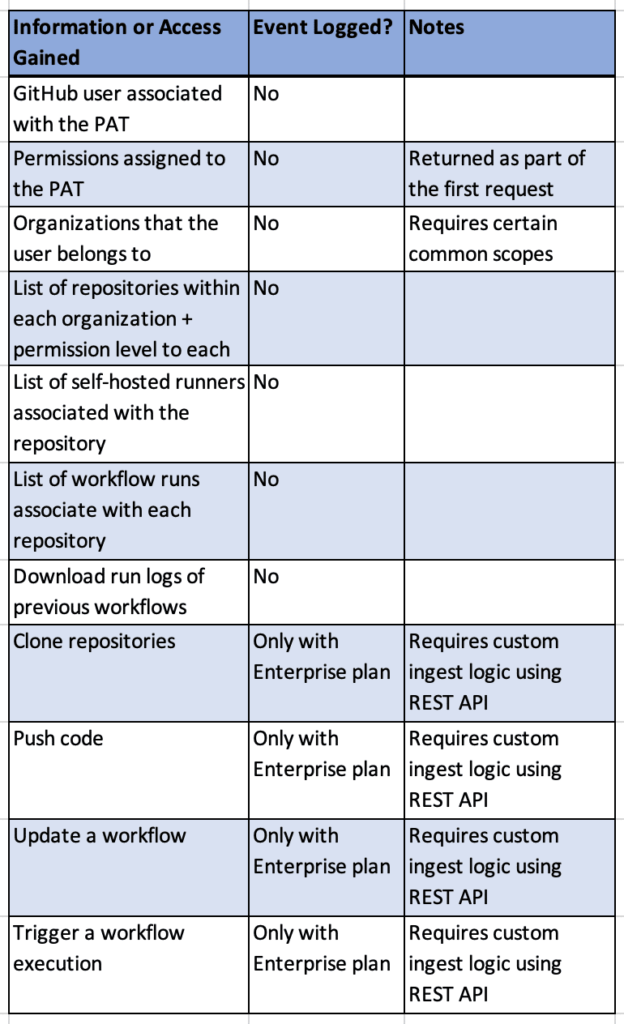
Overview Continuous Integration and Continuous Delivery (CI/CD) systems are powerful and configurable tools within modern environments. At Praetorian, we are seeing organizations migrate to SaaS solutions like GitHub (GitHub.com) as their source code management and CI/CD solution, instead of on-premises tools like BitBucket, Bamboo, and Jenkins. On our Red Team engagements , we routinely employ […]
Six Months of Finding Secrets with Nosey Parker
Earlier this year we announced Nosey Parker, a new scanner that uses machine learning techniques to detect hardcoded secrets in source code with few false positives. Since then we’ve continued its development and expanded its use in security engagements at Praetorian. In a few cases Nosey Parker has contributed to critical-severity findings, such as complete […]
Introducing FingerprintX: The fastest port fingerprint scanner

Introduction Port fingerprinting can detect specific services running on a network, which makes it useful during penetration tests. It expands visibility into potential attack surfaces and vulnerabilities within the network environment. Over the summer, our interns worked towards developing a new tool for port fingerprinting services: Fingerprintx Fingerprintx is a port fingerprinting utility tool useful […]
Safeguarding Memory in Higher-Level Programming Languages
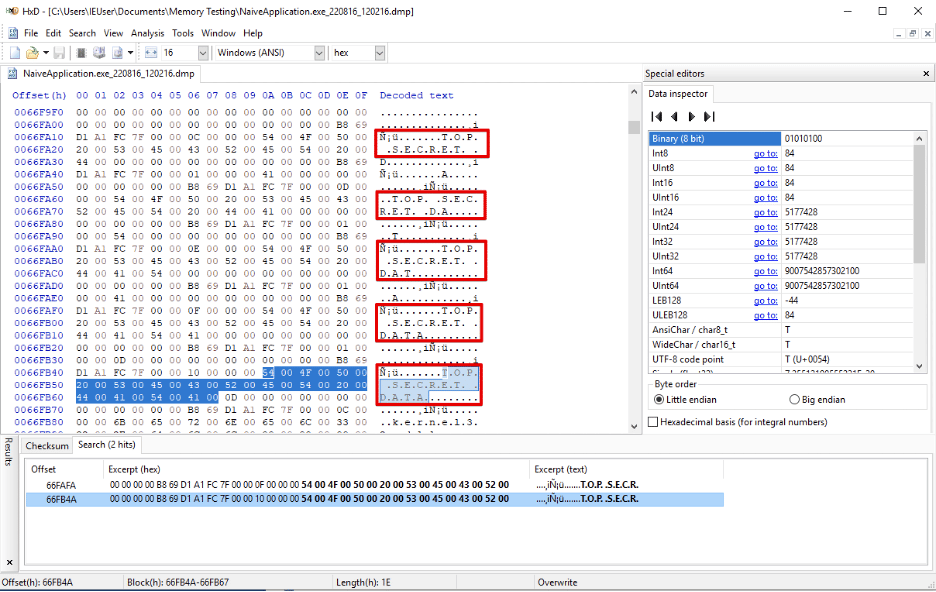
Consider an application written in a higher-level language like Python, NodeJS, or C#. This application must handle sensitive data such as banking credentials, credit card data, health information, or network passwords. The application developers have already hardened the application against malicious users and are confident that it is not vulnerable to database injections, account takeovers, […]
Whitebox Security Assessments: Doing More with More
When deciding on what type of security assessment to get, an organization should consider how much information they are willing to share. Several types of assessments exist, and the key differentiator is how much access an organization grants the testers from the beginning. The terms blackbox, greybox, and whitebox refer to whether a client chooses […]