Continuous Threat Exposure Management for Google Cloud

On July 9th, 2020, an independent security firm discovered a trove of personal health information belonging to Pfizer patients on the public internet. The breach exposed unencrypted conversations between patients and providers of four different Pfizer products, including full names, home addresses, email addresses, phone numbers, and medical status details. The entry point of this […]
Attack Surface Management: A Free Enablement Technology for Effective Continuous Threat Exposure Management
As digital landscapes continue to evolve daily, organizations are increasingly aware and focused on their attack surfaces to identify and mitigate potential risks. However, a troubling trend has emerged: companies are often compelled to pay bug hunters for exploiting vulnerabilities based on surface-level discoveries. At Praetorian, we challenge this norm by offering a free version […]
Secrets Exposed: The Rise of GitHub as an Attack Vector

A Look at Chariot’s Capability to Protect On June 6, 2024, an anonymous user posted nearly 300 GB of stolen source code to 4chan. Per the user, the leak contained “basically all source code belonging to The New York Times”. The NYT later confirmed the leak and said the root case was an exposed GitHub […]
CVE-2024-6387: RegreSSHion
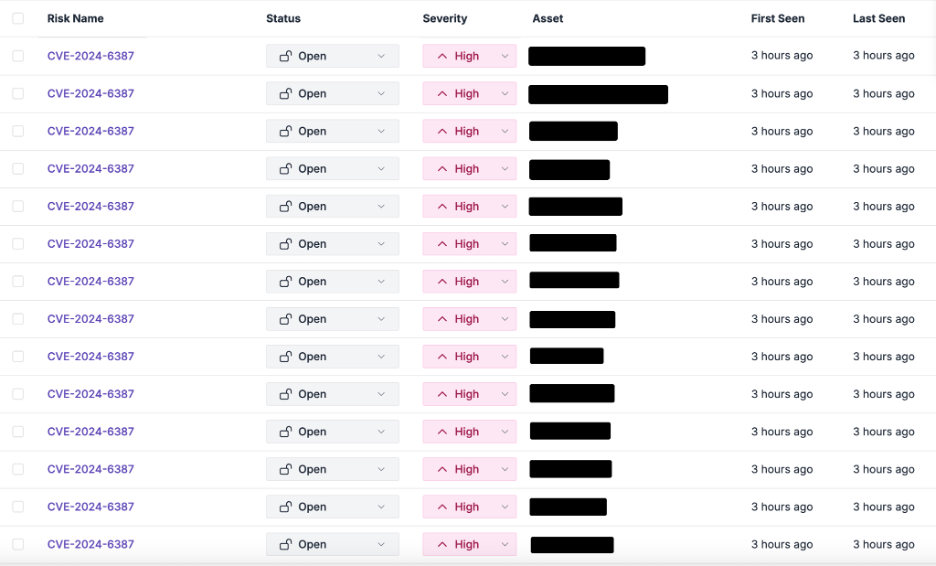
July 5th, 2024 Update Chariot detected numerous instances of CVE-2024-6387 in our customers’ environments this week. We have notified all of our impacted customers to begin the remediation process. On July 1, 2024, the Qualys Threat Research Unit (TRU) announced an unauthenticated remote code execution in OpenSSH’s sshd server. Cataloged as CVE-2024-6387, the vulnerability is […]
Chariot Continuous Threat Exposure Management (CTEM) Updates
Our engineering team has been hard at work, reworking our flagship Chariot platform to remain the most comprehensive and powerful CTEM platform on the market. So what’s new? Here are several new features recently added to Chariot: 1. Unmanaged Platform Chariot, Praetorian’s Continuous Threat Exposure Management (CTEM) solution, is now available as a self-managed platform. Organizations can […]
Compromising ByteDance’s Rspack using GitHub Actions Vulnerabilities
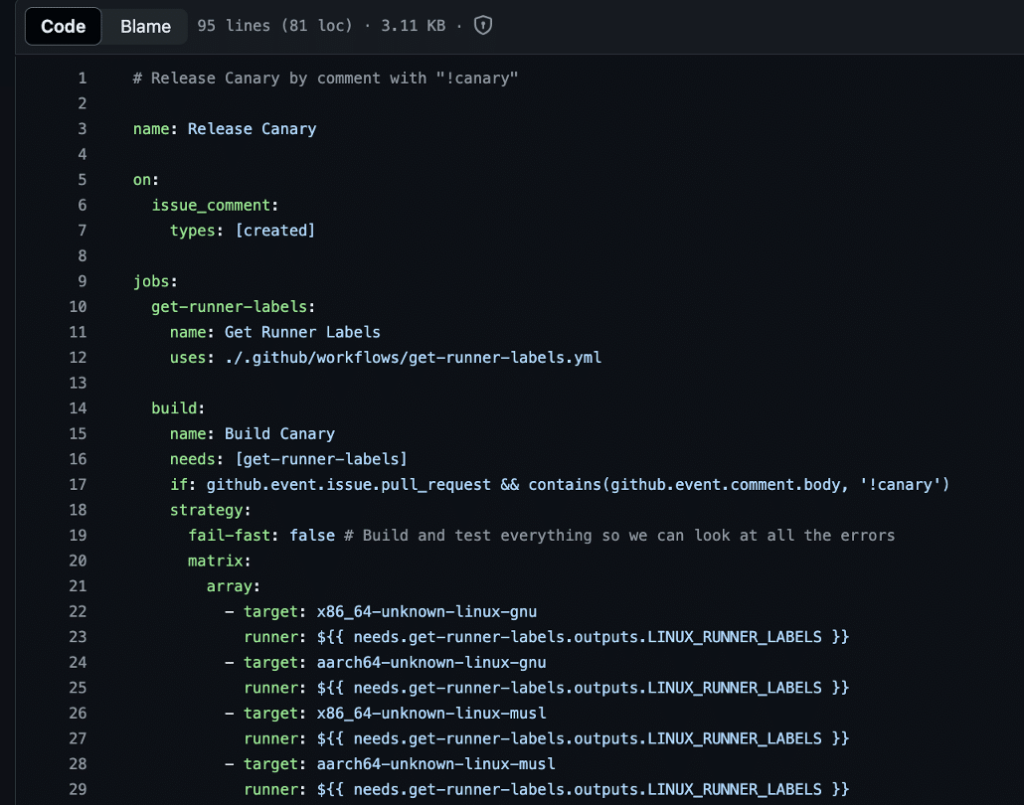
Recently, we identified several critical Pwn Request vulnerabilities within GitHub Actions used by the Rspack repository. These vulnerabilities could allow an external attacker to submit a malicious pull request, without the requirement of being a prior contributor to the repository, and compromise the following secrets…
Local Privilege Escalation Vulnerability in Ant Media Server (CVE-2024-32656)
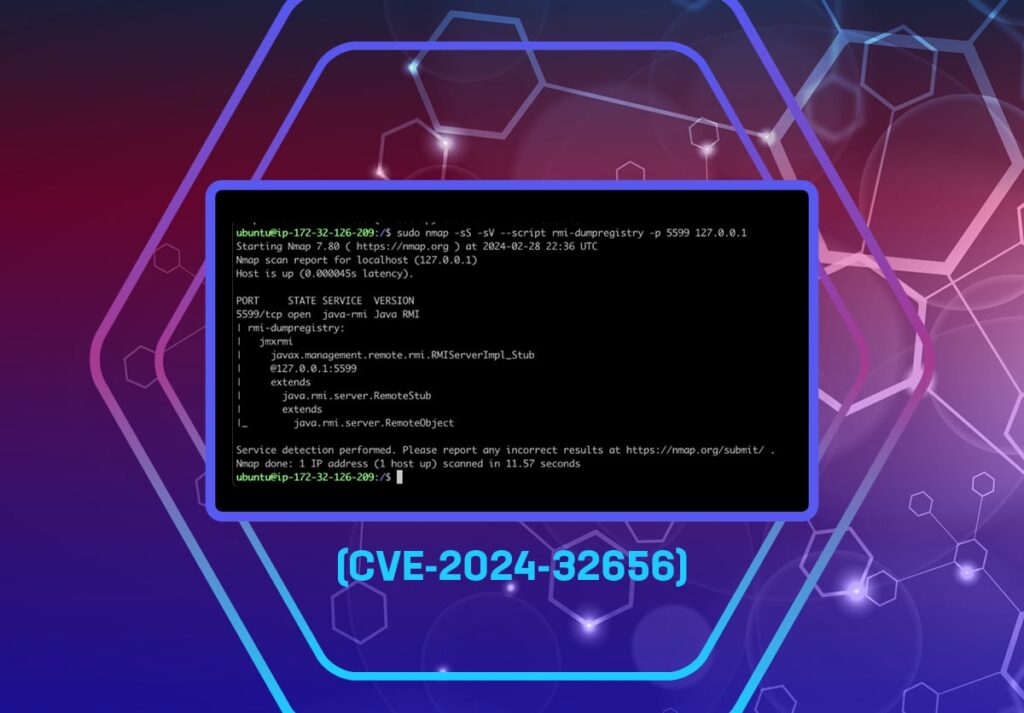
Overview In an effort to safeguard our customers, we perform proactive vulnerability research with the goal of identifying zero-day vulnerabilities that are likely to impact the security of leading organizations. Recently, we decided to take a look at Ant Media Server with the goal of identifying any vulnerabilities within the application. We performed testing against […]
MeshCentral Cross-Site Websocket Hijacking Vulnerability (CVE-2024-26135)

Overview In this article we discuss a recent cross-site websocket hijacking (CSWSH) vulnerability that we identified in MeshCentral, a web-based remote monitoring and endpoint management solution. MITRE assigned the CVE identifier CVE-2024-26135. End users can use MeshCentral to install agents that communicate with a centralized server. The centralized server then allows users to perform remote […]
Exploiting Kubernetes through Operator Injection

Introduction The Kubernetes documentation describes operators as “software extensions to Kubernetes that use custom resources to manage applications and their components.” These operators automate application resource deployment and management with custom controllers tied to one or more custom resource definitions. Custom controllers create bespoke attack surfaces that attackers can target when they can control custom resource data. […]
Relution Remote Code Execution via Java Deserialization Vulnerability
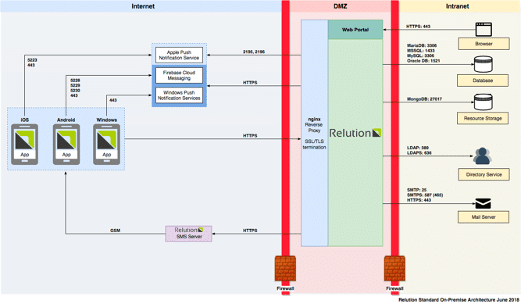
Overview In this article we discuss a recent deserialization vulnerability we found in Relution (CVE-2023-48178), a mobile device management product that is popular among multinational German corporations. CVE-2023-48178 can potentially lead to remote code execution and complete compromise of the MDM application and clients managed by the solution. The deserialization vulnerability exists in a component […]