Ghost Calls: Abusing Web Conferencing for Covert Command & Control (Part 2 of 2)

In part one, we discussed the architecture of web conferencing applications, with a specific focus on Zoom’s architecture to support web conferencing at a massive global scale. Part two will discuss the approach we developed to support tunneling traffic through Zoom and Microsoft Teams using the TURN protocol. Let’s start with a quick recap of […]
Ghost Calls: Abusing Web Conferencing for Covert Command & Control (Part 1 of 2)

In the middle of a particularly tight red team engagement, we hit a familiar wall. Our long-term implant was rock solid—quiet, persistent, and thoroughly under the radar. But when it came time to pivot into something more interactive—proxy traffic, tunnel HVNC, relay NTLM—we started running into limits. The channel that worked so well for low-and-slow […]
Hunting for Secrets in Plain Sight: Leveraging Internal Logging and Monitoring Services
In penetration testing and red teaming, success often lies in uncovering hidden paths of least resistance. While sophisticated exploits and zero-days frequently capture headlines, highly effective attack opportunities often hide in plain sight – like within internal logging and monitoring platforms. At Praetorian, we’ve observed first-hand the value of targeting internal logging and monitoring platforms […]
CI/CD Training from the Front Lines: Offensive Security at Black Hat
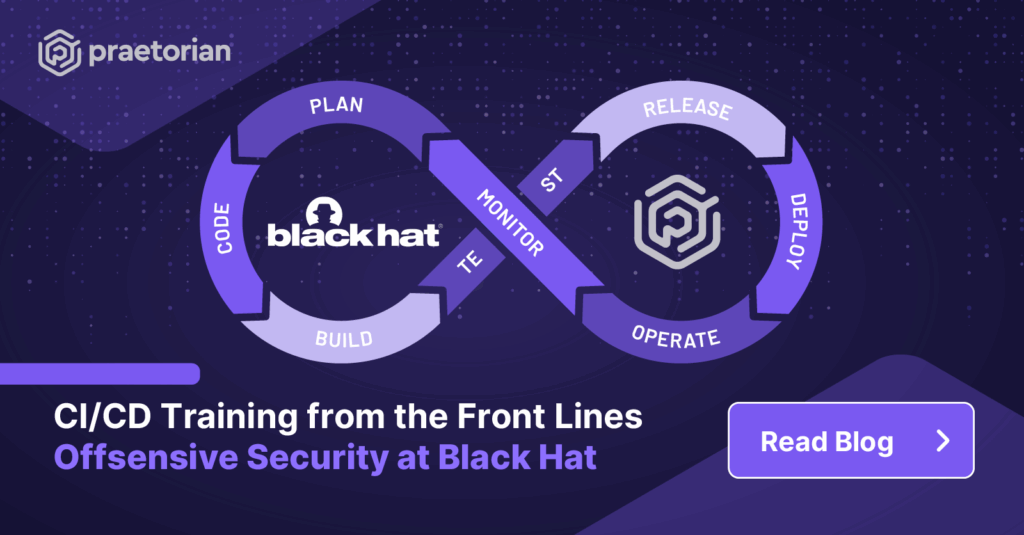
Our Red Team has explored and exploited vulnerabilities in the CI/CD space over the last several years, resulting in numerous successful offensive operations, open-source tool development, and presentations at Black Hat, DEF CON, and Schmoocon. With organizations increasingly relying on automated deployment pipelines, securing CI/CD infrastructure has become more critical than ever — yet many […]
GitPhish: Automating Enterprise GitHub Device Code Phishing
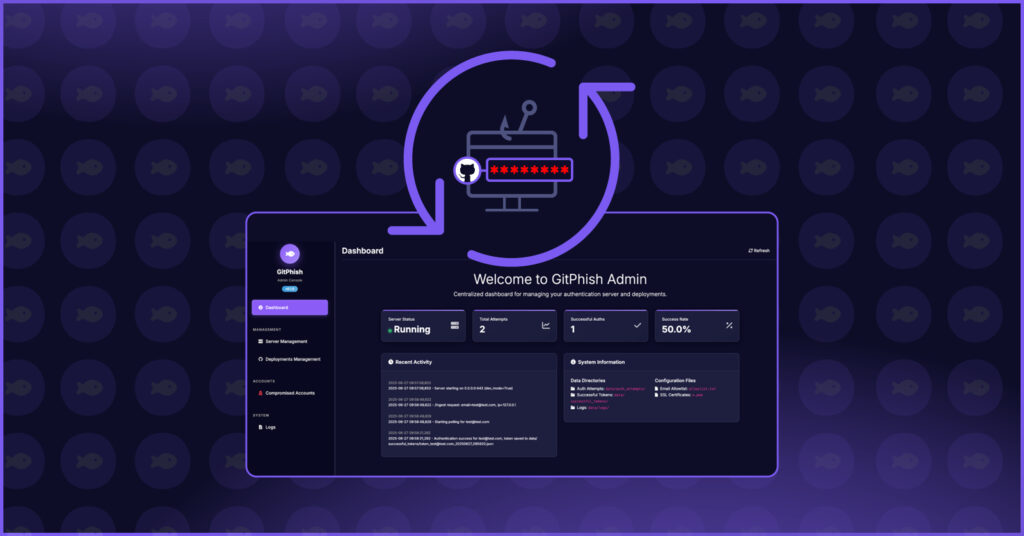
Two weeks ago, we published research on GitHub Device Code Phishing, a simple technique that can turn an eight-digit code and a phone call into a complete compromise of an organization’s GitHub repositories and software supply chain. While the concept is simple, executing these attacks often brings multiple layers of complexity, like building a convincing […]
Introducing: GitHub Device Code Phishing
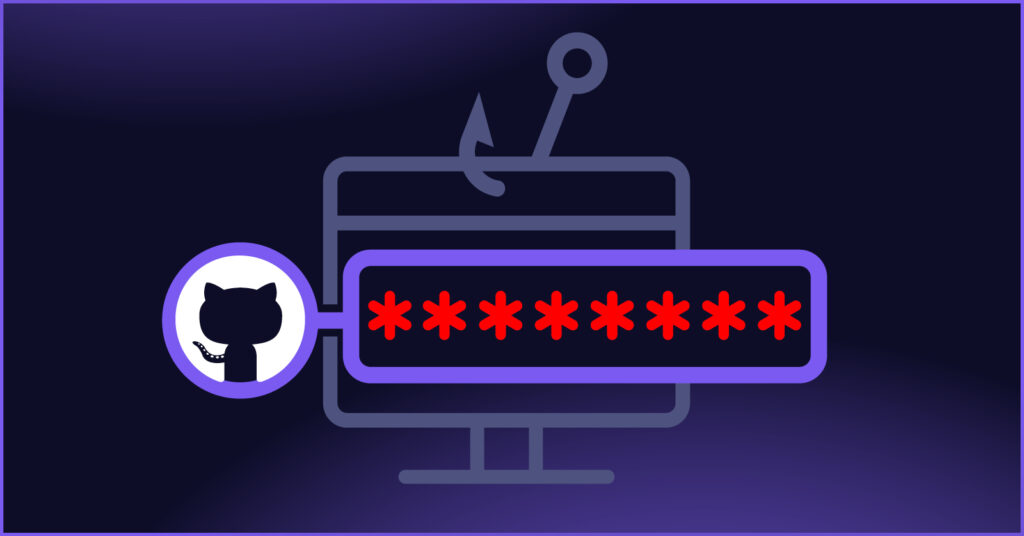
What if all it took to compromise a GitHub organization–and thus, the organization’s supply chain–was an eight-digit code and a phone call? Introducing: GitHub Device Code Phishing. While security teams have been battling Azure Active Directory device code phishing attacks for years, threat actors have overlooked GitHub’s OAuth2 device flow as an attack vector. At […]
Hardware Hacking a Nicotine Vape

Praetorian recently finished a tour de force at Hack Space Con, providing paid training, a workshop, and three talks: The entire Praetorian team had a blast at the conference, sharing our knowledge with the security community and making many new friends. HackVapeCon Before the conference started, four members of Praetorian’s Internet of Things (IoT) team […]
Agent of Chaos: Hijacking NodeJS’s Jenkins Agents
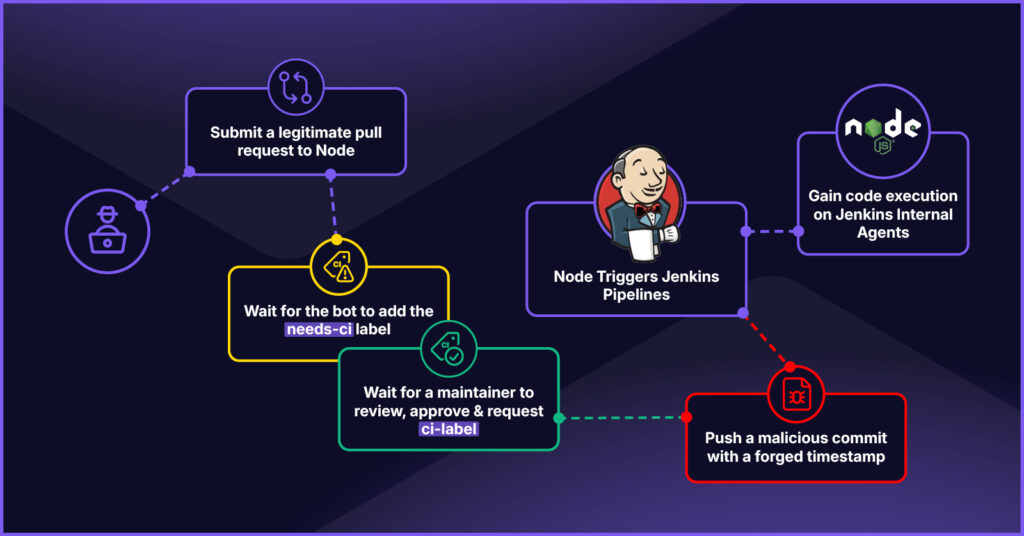
Relationships are complicated. When multiple DevOps platforms work together to execute pipelines for a single GitHub repository, it begs the question: Do these platforms get along? Node.js, the most popular JavaScript runtime in the world, uses a set of triplets to execute its CI/CD pipelines: a GitHub App, GitHub Actions workflows, and Jenkins pipelines. Like […]
ELFDICOM: PoC Malware Polyglot Exploiting Linux-Based Medical Devices
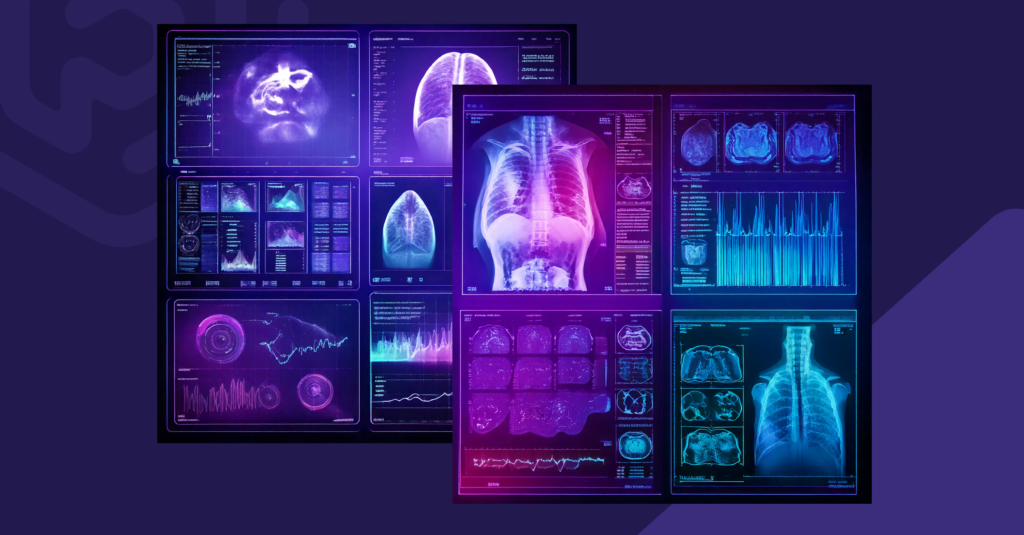
A high severity vulnerability in DICOM, the healthcare industry’s standard file protocol for medical imaging, has remained exploitable years after its initial disclosure. The flaw enables attackers to embed malicious code within legitimate medical image files. While previous research demonstrated this vulnerability’s impact on Windows-based medical systems, Praetorian’s new proof of concept, ELFDICOM, extends the […]
An Improved Detection Signature for the Kubernetes IngressNightmare Vulnerability

Wiz recently published a detailed analysis of a critical vulnerability in the NGINX Ingress admission controller—what they’ve dubbed IngressNightmare (CVE-2025-1097, CVE-2025-1098, CVE-2025-1974, CVE-2025-24514). The vulnerability stems from insufficient input validation during configuration file processing, allowing an attacker to inject arbitrary code into the NGINX process. Wiz’s writeup is excellent and covers the technical nuances thoroughly, […]