Offensive Security
Red Team
Test and exercise your cybersecurity program against real-world attacks. Praetorian Red Team will put your security capabilities through its paces, while leveraging weaknesses across people, process and technology across prevention, detection and response
Overview
A red team exercise validates how well an organization withstands realistic, targeted attacks. Many organizations over-index on vulnerability scans and miss gaps in detection, response, or decision-making under pressure. A focused red team simulates sophisticated adversaries to reveal those gaps and prove the resilience of people, processes, and technology.
Why Run a Red Team?
Organizations face complex threats that combine technical exploits with social engineering and operational manipulation. A red team goes beyond automated checks and evaluates whether your defenses stop an attacker who adapts in real time. That evidence helps boards, CISOs, and security teams make prioritized investments and improve incident playbooks.
Results from red-team exercises typically show gaps in detection latency, escalation procedures, and third-party trust assumptions. Those findings inform risk prioritization and help justify budget decisions to stakeholders.
Simulate Sophisticated Attacks to Strengthen Your Defenses
Praetorian’s red‑team engagements immerse your organization in a realistic cyber‑attack. Rather than running a purely theoretical tabletop exercise, we emulate the tactics of nation‑state adversaries and advanced persistent threats to expose weaknesses across your people, processes and technology. Each engagement is tailored to your business objectives and risk profile – from protecting customer data to safeguarding critical infrastructure – and is delivered by a team of ex‑NSA, CIA and elite security researchers. This precision and expertise are essential in cybersecurity marketing because buyers want technically sound content that converts into meaningful action
Our red‑team services are not just about finding vulnerabilities; they are designed to help you prove the resilience of your security program, validate playbooks, and prioritise investments. Through expert‑driven content and clear communication, we build the trust that decision‑makers demand
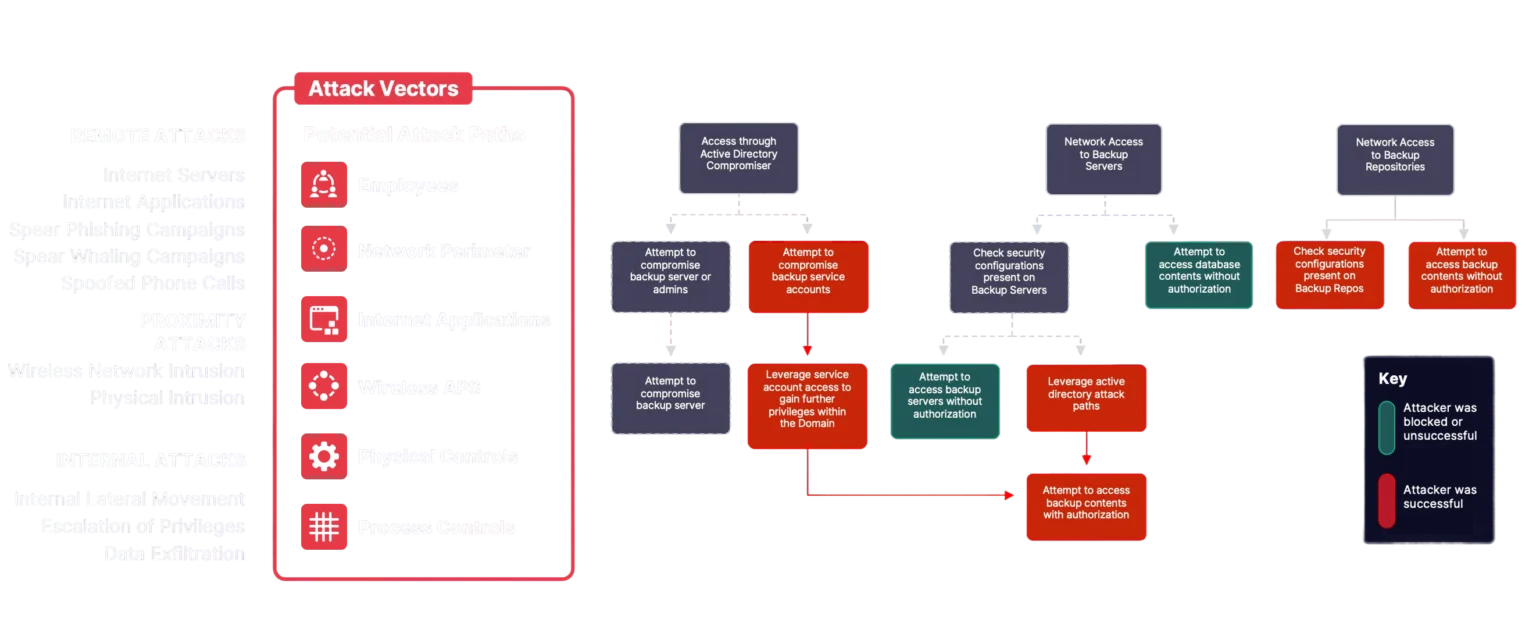
Common Red Team Attack Objectives
Demonstrate direct financial loss through the transfer of monetary funds to a nominated bank account
Demonstrate access to VIP mailbox, data, or workstation
Demonstrate ability to exert control over an ICS device or environment [water plant, food processing, oil refinement]
Demonstrate control over a critical capability such as power supply to a geographic location
Simulate ransomware attack by encrypting test systems and demanding a ransom
Perpetrate theft of intellectual property (IP) and competitive differentiation or theft of customer data such as PII, PHI, or CC information
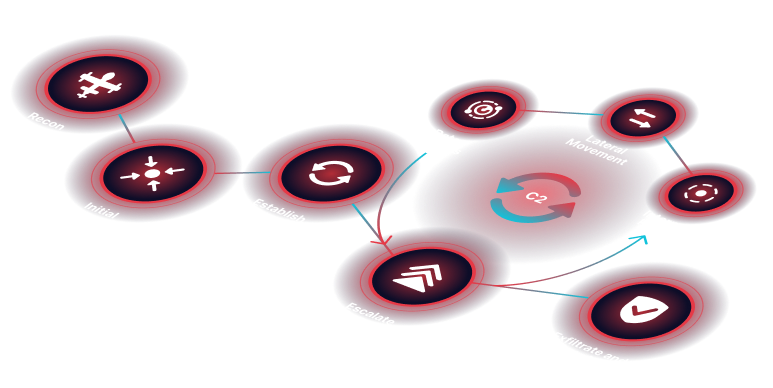
Red Team Attack Lifecycle
Attack Staging
Prepare the infrastructure and tooling required to orchestrate the attack
Reconnaissance
Obtain information about the client’s people, process, and technology to identify attack surfaces and provide intelligence to attacks
Initial Access
Identify and exploit attack vectors to gain initial access to the target environment
Persistence
Establish a persistent foothold within the target environment
Lateral Movement
Compromise additional assets and gain additional privileges in a strategic fashion that supports the attack mission
Privilege Escalation
Compromise additional assets and gain additional privileges in a strategic fashion that supports the attack mission
Actions on Objectives
Understand the standard operating procedures surrounding the attack objectives and perform necessary steps to achieve the goal
Why Praetorian?
Expert Offensive Security Engineers
Our core operators are former NSA and CIA officers and top-tier security researchers with decades of offensive experience. They simulate nation-state attack patterns and advanced persistent threats (APTs) to give your organization a realistic assessment of sophisticated adversary operations.
Cutting-Edge Offensive Security Research
A dedicated offensive labs research team continuously develops new tactics, techniques, and procedures (TTPs), creates bespoke covert tools, and discovers zero-day exploits. This emergent attack intelligence ensures your red-team assessment stays ahead of the evolving threat landscape.
Praetorian Guard™ Red Team Platform
Our proprietary platform provides a centralized focal point for managing red-team engagements, tracking attack objectives, and demonstrating the real-world impact of security weaknesses. It enables continuous adversarial exposure validation to help you find the breach point before an actual compromise occurs.
Close Collaboration With White Team
We work closely with stakeholders to set objectives, define rules of engagement, and establish a threat model. Throughout the exercise, we maintain open communication with designated defensive teams to ensure an in-depth debrief and actionable program improvement.
How Praetorian’s Red Team Will Work with You
Engagements begin with a kickoff to align objectives, scope, and rules of engagement. Clear communication ensures the exercise tests critical business risks without disrupting operations. Our teams iterate through planning, execution, and debrief so defenses can be exercised and improved. After the live exercise we deliver a debrief and a remediation plan that security teams can operationalize. We also recommend aligning results with established frameworks such as the NIST Cybersecurity Framework to make remediation measurable and repeatable.
Project Kickoff
Praetorian’s Practice Manager will set up a kickoff call with client stakeholders to introduce the team.
Rules of Engagement and Threat Model
We explicitly determine the scope of the exercise and collaboratively define the attack objective.
Red Team Excercise
Our engineers execute the end-to-end attack lifecycle. Communications occur between the predefined teams in a fluid fashion.
Technical Report
Upon completion of the live exercise, Praetorian compiles the draft report.
Executive Presentation
We hold a debriefing call between all participants and the client’s project stakeholders wherein we discuss an in-depth narrative of the exercise.

Deliverables
Deliverables are tailored to stakeholder needs and typically include a technical report, executive summary, and a prioritized remediation roadmap. The goal is to translate technical findings into business impact and measurable improvements.
- Technical narrative of the attack chain with forensic artifacts
- Executive-level risk assessment for leadership
- Playbook validation and recommendations for detection and response
Clients often use these deliverables to validate security investments, support audits, and demonstrate regulatory due diligence. For further reading on threat modeling and frameworks, see the MITRE ATT&CK knowledge base.
Who Needs this Service
Boards of Directors
Seeking to ascertain the risk of a high profile attack and understand potential impacts to the business, its customers, and partners.
Security teams
Wanting to run their playbooks or justify new security initiatives, budget cycles, or recent security investment
Organizations
Needing to demonstrate resilience against cyber-attacks and/or demonstrate resolution of audit findings as part of previous engagements or regulatory requirements
Frequently Asked Questions
A penetration test typically focuses on finding and exploiting technical vulnerabilities. A red team simulates an adaptive adversary across people, process, and technology to test detection and response in realistic scenarios.
Durations vary by scope but most engagements run from two to six weeks including planning, execution, and reporting. Timeline depends on objectives, environment complexity, and approved rules of engagement.
Red teams operate under strict rules of engagement and safety constraints to avoid unintended disruption. Simulated destructive actions are performed only on isolated test systems or with prior approval.
Success is measured by whether the engagement met predefined objectives, improved detection and response times, and produced actionable remediation prioritized by business impact.
Ready to Discuss Your Red Team Initiative?
Praetorian’s Offense Security Experts are Ready to Answer Your Questions