Which Came First: The System Prompt, or the RCE?

During a recent penetration test, we came across an AI-powered desktop application that acted as a bridge between Claude (Opus 4.5) and a third-party asset management platform. The idea is simple: instead of clicking through dashboards and making API calls, users just ask the agent to do it for them. “How many open tickets do […]
Azure APIM Signup Bypass: 97.9% of Developer Portals Still Exploitable Anonymously and from the Internet
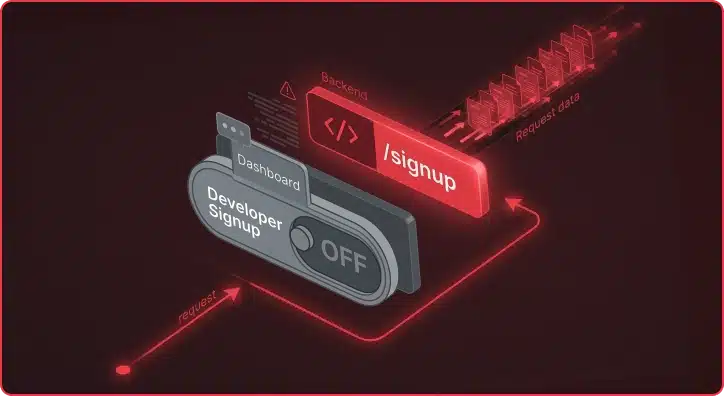
The Azure APIM signup bypass is a critical vulnerability affecting 97.9% of internet-facing Developer Portals. Azure API Management (APIM) exposes APIs to external consumers through a Developer Portal, the interface where developers self-register, obtain API keys, and make API calls. The default APIM configuration ships with Basic Authentication enabled as the identity provider and the […]
When HttpOnly Isn’t Enough: Chaining XSS and GhostScript for Full RCE Compromise
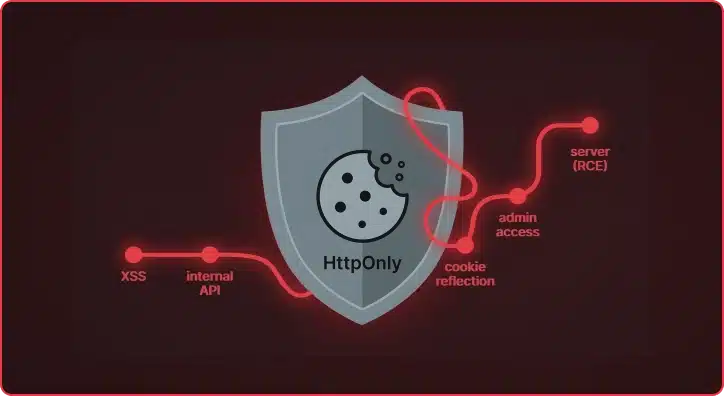
What started as a standard cross-site scripting vulnerability in a document processing platform turned into a full administrative takeover of the application and, ultimately, remote code execution on the underlying server. The HttpOnly flag protected the session cookie from Javascript, but did the application keep it safe? During a recent assessment of a document processing […]
Et Tu, RDP? Detecting Sticky Keys Backdoors with Brutus and WebAssembly

Everyone knows that one person on the team who’s inexplicably lucky, the one who stumbles upon a random vulnerability seemingly by chance. A few days ago, my coworker Michael Weber was telling me about a friend like this who, on a recent penetration test, pressed the shift key five times at an RDP login screen […]
When Proxies Become the Attack Vectors in Web Architectures
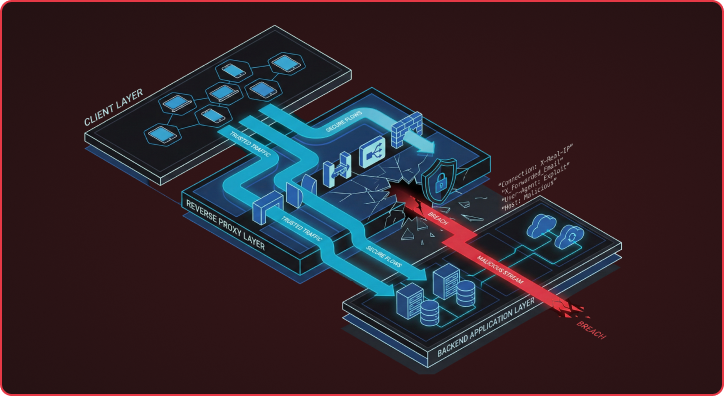
Many Reverse proxy attack vectors expose a flawed assumption in modern web architectures that backends can blindly trust security-critical headers from upstream reverse proxies. This assumption breaks down because HTTP RFC flexibility allows different servers to interpret the same headers in fundamentally different ways, creating exploitable gaps that attackers are increasingly targeting. I want to […]
Beyond Prompt Injection: The Hidden AI Security Threats in Machine Learning Platforms
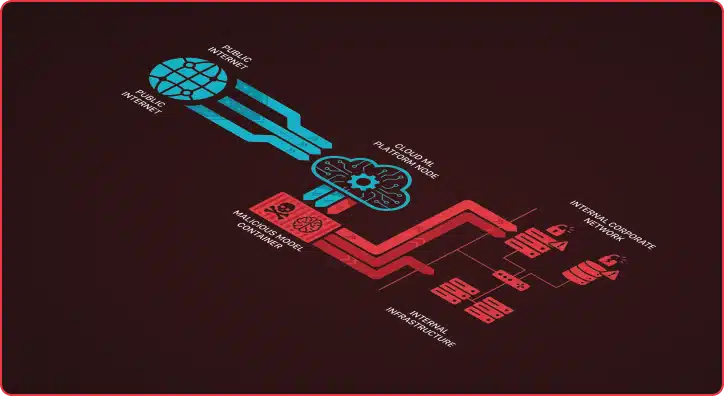
What’s the first thing you think of when you hear about AI attacks and vulnerabilities? If you’re like most people, your mind probably jumps to Large Language Model (LLM) vulnerabilities—system prompt disclosures, jailbreaks, or prompt injections that trick chatbots into revealing sensitive information or behaving in unintended ways. These risks have dominated headlines and security […]
How AI Agents Automate CVE Vulnerability Research

The CVE Researcher is a multi-agent AI pipeline that automates vulnerability research, detection template generation, and exploitation analysis. Built on Google’s Agent Development Kit (ADK), it coordinates specialized AI models through four phases — deep research, technology reconnaissance, actor-critic template generation, and exploitation analysis — to produce production-ready Nuclei detection templates overnight. Beyond Simple Automation […]
AI-Powered CVE Research: Winning the Race Against Emerging Vulnerabilities
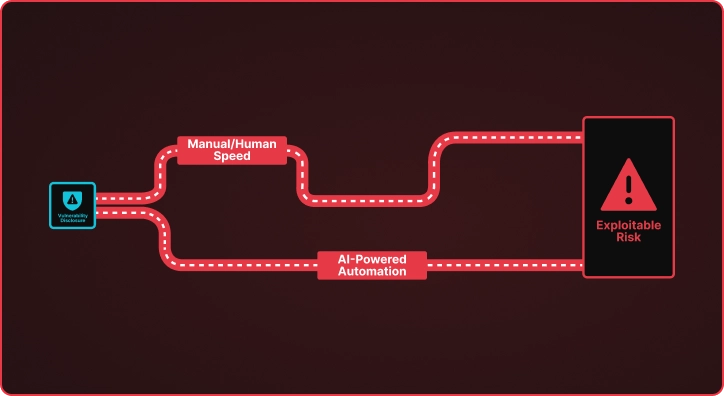
The Vulnerability Time Gap When CISA adds a new CVE to the Known Exploited Vulnerabilities catalog, a clock starts ticking. Security teams must understand the vulnerability, determine if they are exposed, and deploy detection mechanisms before adversaries weaponize the flaw. This process traditionally takes days or weeks of manual research by skilled security engineers who […]
Gone Phishing, Got a Token: When Separate Flaws Combine

TL;DR: Two medium-severity flaws, an unsecured email API endpoint and verbose error messages exposing OAuth tokens, chain together to enable authenticated phishing that bypasses all email security controls, persistent access to Microsoft 365 environments, and full infrastructure compromise. Neither flaw alone would be critical; combined, they’re devastating. Modern web applications increasingly create attack surfaces through […]
Corrupting the Hive Mind: Persistence Through Forgotten Windows Internals
Eventually after you write a tool, the time comes to make it public. That time has come for Swarmer, a tool for stealthy modification of the Windows Registry as a low privilege user. It’s been almost a year since we first deployed this technique in the wild, and given enough time has passed, it seems appropriate […]