Log4j Update: False Negatives and Additional Recommendations

We had a busy weekend here at Praetorian. Following the initial disclosure of the Log4j (Log4Shell)* vulnerability, we’ve added a capability to identify the issue to our attack surface enumeration tool. As we scanned production environments for the vulnerability over the weekend we’ve learned a lot more about how the issue can actually look in […]
Log4j: It’s worse than you think

On December 9th, 2021, a new 0-day vulnerability in the popular Java logging package log4j v2.x was announced. The vulnerability is particularly unpleasant as exploitation frequently requires only the ability to cause the system to log an attacker controlled string to a vulnerable logging instance. Thus, the routes of exploitation are broad and often require […]
Introducing Snowcat: World’s First Dedicated Security Scanner for Istio

Why Service Meshes Matter Over the last few years, the pace of moving workloads to the cloud has continued to accelerate. Mostly, this has been a boon for innovation, allowing complex monolithic on-prem instances to be broken into microservice architectures, which provide decoupling, agility, and stability. From a development perspective, life has in some ways […]
How to Detect and Dump Credentials from the Windows Registry

There are several post-exploitation techniques that an attacker can utilize to gather information and compromise assets. One of these techniques is OS credential dumping, and some relevant areas of interest are the Windows Registry and the LSASS process memory. By obtaining additional credentials, an attacker could look to move laterally in the environment by utilizing […]
Introducing GoKart, a Smarter Go Security Scanner
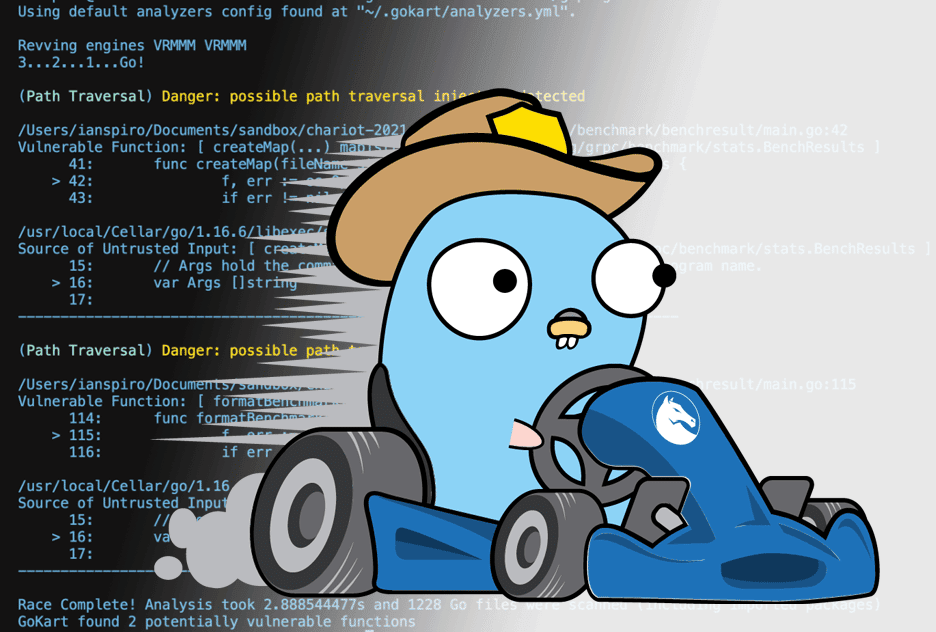
At Praetorian, we’re committed to promoting and contributing to open source security projects and radically focused on developing technologies to enhance the overall state of cybersecurity. We love when our passions and business commitments overlap so today we’re stoked to announce the initial release of GoKart – a smarter security scanner for Go. GoKart is […]
Attacking and Defending OAuth 2.0 (Part 2 of 2: Attacking OAuth 2.0 Authorization Servers)

Introduction The OAuth 2.0 authorization framework is designed to improve security by delegating limited access to third-parties without sharing credentials. In our previous blog post on OAuth 2.0 we discussed how OAuth 2.0 implementations should be secured. Unfortunately, it is common for vulnerabilities to be introduced with OAuth 2.0 implementations, particularly on the side of […]
A New Tool for Password Spraying Emulation

This article introduces Trident, an open-source cybersecurity tool for emulating password spraying.
Attacking and Defending OAuth 2.0 (Part 1 of 2: Introduction, Threats, and Best Practices)

First of a two-part series discussing OAuth 2.0 from the perspective of a security engineer in both an offensive and defensive role
Solving Cybersecurity’s Hardest Problems with Machine Learning

This article provides a glimpse into some of the groundbreaking work that the experts at Praetorian are undertaking, applying Machine Learning to solve some of the industry’s most challenging problems.
What is Threat Modeling, and Why it’s Important

What is Threat Modeling, why it’s valuable to organizations, and when it should be used?