Broadcast Name Resolution Poisoning / WPAD Attack Vector
One of the common attack vectors for penetration testing is to leverage an attack known as Broadcast Name Resolution Poisoning. Recently, US-CERT posted an advisory about this attack being used externally. Attackers purchased new generic Top-Level Domains (gTLDS) and setup entries for the Web Proxy Auto-Discovery Protocol (WPAD). This is pretty interesting since it’s an old attack used in a new way. Let’s dive into how Broadcast Name Resolution Poisoning is used during internal penetration testing and go over recommendations for how to fully mitigate all forms of attack.
JTAGulator vs. JTAGenum, Tools for Identifying JTAG Pins in IoT Devices
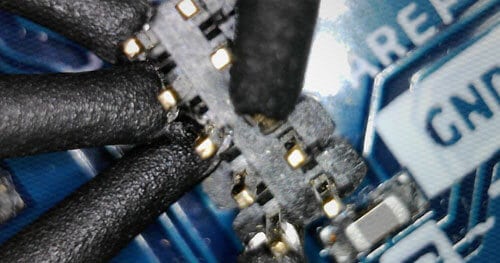
Do you suspect some pins on your device are JTAG? There are several methods out there for identifying if pins are likely to be JTAG or not. One of those methods involves buying a $200 JTAGulator, however there is a cheaper Arduino-based alternative I will be detailing in this post. First I’ll explore the expensive way.
Why are JTAG and UART still effective attack vectors for IoT devices?
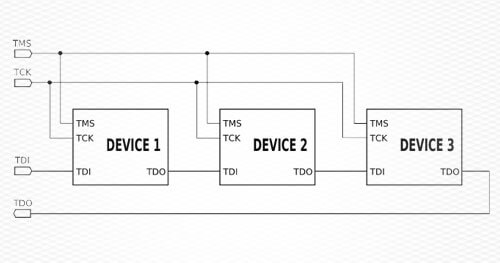
Whether it’s a vulnerable router, an Internet of Things (IoT) connected device, or some other piece of hardware, JTAG and UART debugging test pins left on the device are going to continue to be one of the most effective physical hardware attack vectors available to a malicious actor. Never assume your secrets on IoT devices, such as encryption keys, are safe. You may be wondering what JTAG and UART are, and why they’re left on boards.
Internetwache RE60 Writeup: Symbolic Execution Tramples CTF Challenge
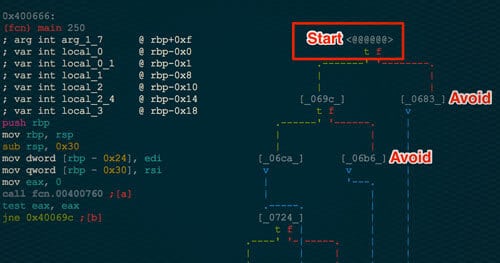
I am always looking for problems that symbolic execution could be applied to in the capture the flag space. This past weekend, this challenge was met during the Internetwache CTF for its RE60 problem. Below I describe the application of symbolic execution to solve the challenge without much knowledge of the inner workings of the binary itself. Symbolic Execution gives the reverse engineer the ability to find a specific path from Point A to Point B in a binary. This path is represented by a series of boolean expressions. These expressions can then be passed to a solver such as Z3 from Microsoft to solve the equation, creating an input that will exercise the found path.
Pentestly Framework: When Pentesting Meets Python and Powershell

Python appears to be an ever growing trend in the security community. Being able to connect Python tools together has proven beneficial for us. Powershell has also seen increasingly more use due to its wide availability in internal environments. Pentestly utilizes the power of these tools together in a familiar user experience.
Hob0Rules Released: Statistics Based Password Cracking Rules
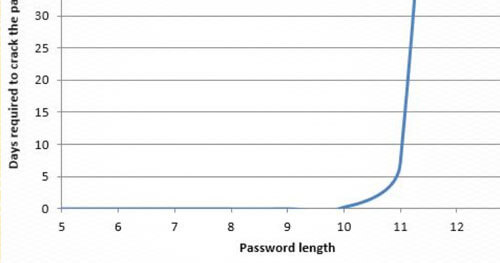
It’s now 2016 and people are still decisively using poor, predictable passwords. Employees around the world will soon be appeasing their mandatory 90-day password rotation by changing their password from ‘Winter2015’ to ‘Spring2016’. This happens in nearly every company – you would be surprised. Previously, I conducted password research to determine common traits of passwords, which was presented at various conferences. The password cracking rules that Praetorian utilizes for all hash cracking have now been released for Hashcat (described below) which are based on these findings. A quick compromise list of 64 of these rules have been released as hob064 and a more extensive ruleset has been released as d3adhob0 for public use. These rulesets were made to compete against their industry standard counterparts, Best64 and d3ad0ne. Both of the released rulesets have bypassed their counterpart in both time speed and number of hashes cracked and will continue to improve. The two sets of rules are living lists and change as the environment of passwords changes.
Ruby Unsafe Reflection Vulnerabilities
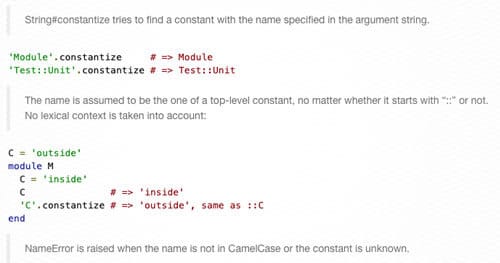
One of the interesting properties of Ruby is the fact that everything is an object. The manipulation of objects at runtime is what makes Ruby so flexible and interesting as a language. At its heart, this is the idea behind reflection. Reflection is a tool to allow a program to examine and modify its own behavior at runtime, granting programmers the ability to simpilify certain constructs (e.g. framework development, dependency resolution).
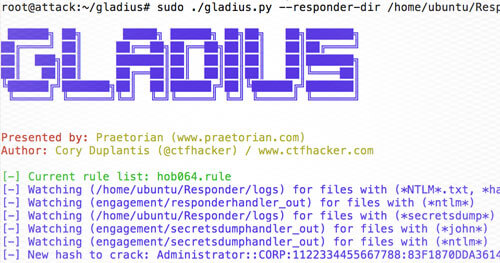
Gladius: Automatic Responder Cracking
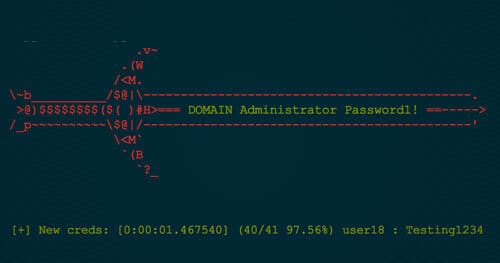
So there you are, performing your internal penetration test, using Responder to potentially grab hashed credentials and thinking "Responder is awesome… but manually cracking credentials isn’t fun." Well, welcome Gladius! Gladius happily listens for Responder hashes (and.. spoiler alert.. secretsdump.py and hashdump) and automatically passes them to hash cat. At its core, Gladius listens in target directories for file events and then performs computations based on the event. Let’s walk through the Responder workflow with Gladius.
Introducing MitM-VM & Trudy: A Dead Simple TCP Intercepting Proxy Tool Set
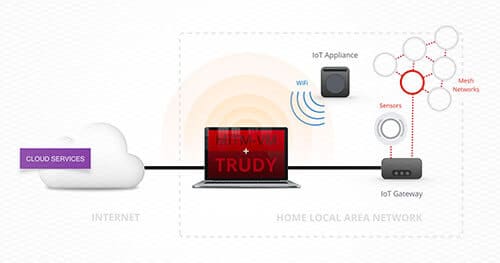
Positioning yourself as a man-in-the-middle (MitM) is a powerful situation to leverage during a security assessment. Unfortunately, in some situations, leveraging an active MitM position is difficult. There are existing proxies that try to alleviate these issues but they all seem to suffer from a flaw that makes using the tool undesirable. MitM-VM and Trudy are a complimentary set of tools that are designed to address several issues with existing proxies. Together they enable easy-to-setup and powerful man-in-the-middle positions. Why build these tools? Modifying custom binary protocols on the fly while sitting between an embedded device and a server is usually a slow process that involves sniffing legitimate traffic and then rebuilding packets programmatically. Trudy makes this process easy by enabling Burp-like features for generalized TCP traffic.
The Reason My Lamp is Insecure

I suffer the struggle many others do. It’s a systemic issue that’s not really talked about much. The issue I’m talking about is the inconvenience of turning my lamp off and then proceeding to stumble around in the dark to get to my bed. I set out to solve this problem by automating my lamp with a Raspberry Pi, a relay, and a simple web application. Those who have worked with electronics before know this setup is not very technically challenging, but I wasn’t going for anything too fancy. My goal was to create a simple web application that could turn my lights on and off, which can be seen in the code below. This code also includes an alarm clock which operates by flashing my lights every morning at a preset time.