The Attack Helix: Praetorian’s AI & Economic Architecture for Offensive Security

The Kill Chain models how an attack succeeds. The Attack Helix models how the offensive baseline improves. The Tipping Point One person. Two AI subscriptions. Ten government agencies. 150 gigabytes of sovereign data. In December of 2025, a single unidentified operator used Anthropic’s Claude and OpenAI’s ChatGPT to breach the Mexican government agencies and a financial institution. […]
A Possible Solution to the Zodiac Killer Z32 Cipher
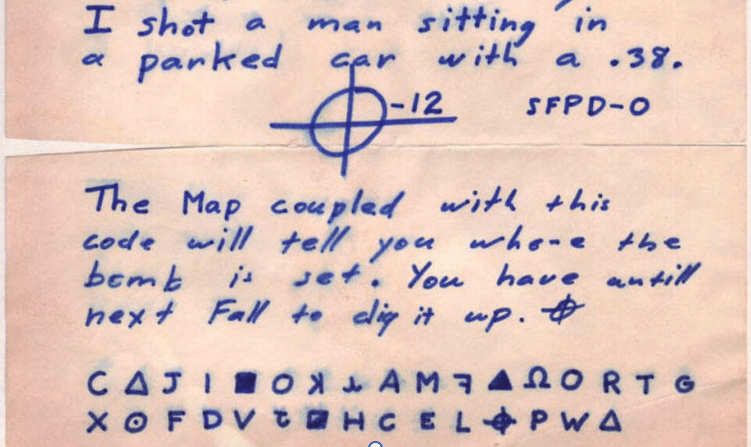
Introduction The Zodiac Killer, one of America’s most notorious unsolved serial killer cases, sent numerous encrypted messages to newspapers during his reign of terror in the late 1960s and early 1970s. While his 408-character cipher was eventually cracked, the shorter “Z32” cipher that accompanied a map of the San Francisco Bay Area has remained unsolved […]
Introducing Augustus: Open Source LLM Prompt Injection Tool
From LLM Fingerprinting to LLM Prompt Injection Last month we released Julius, a tool that answers the question: “what LLM service is running on this endpoint?” Julius identifies the infrastructure. But identification is only the first step. The natural follow-up: “now that I know what’s running, how do I test whether it’s secure?” That’s what […]
Deterministic AI Orchestration: A Platform Architecture for Autonomous Development
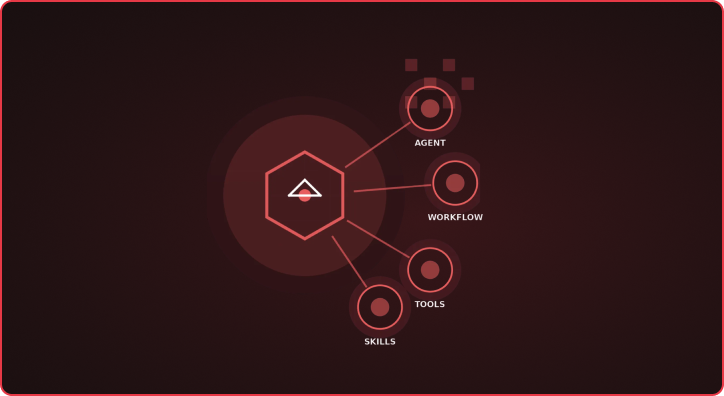
Executive Summary The primary bottleneck in autonomous software development is not model intelligence, but context management and architectural determinism. Current “Agentic” approaches fail at scale because they rely on probabilistic guidance (prompts) for deterministic engineering tasks (builds, security, state management). Furthermore, the linear cost of token consumption versus the non-linear degradation of model attention creates a “Context Trap” […]
Critical Advisory: Remote Code Execution in Next.js (CVE-2025-66478) with Working Exploit

Date: December 4, 2025Severity: Critical (CVSS 10.0)Components: Next.js App Router & React Server Components We are alerting all customers to a critical Remote Code Execution (RCE) vulnerability affecting Next.js applications using the App Router. This vulnerability, tracked as CVE-2025-66478, stems from an upstream issue in the React Server Components (RSC) protocol (CVE-2025-55182). React provided a […]
Introducing Goffloader: A Pure Go Implementation of an In-Memory COFFLoader and PE Loader
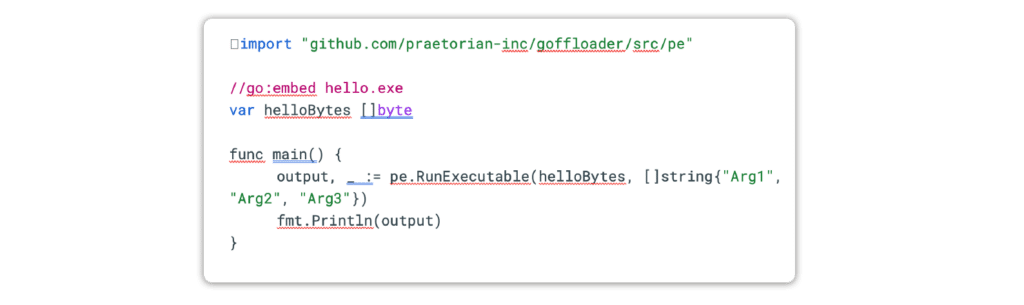
We are excited to announce the release of Goffloader, a pure Go implementation of an in-memory COFFLoader and PE loader. This tool is designed to facilitate the easy execution of Cobalt Strike BOFs and unmanaged PE files directly in memory without writing any files to disk. Goffloader aims to take functionality that is conventionally within […]