CVE-2026-3630: Critical Buffer Overflow in Delta Electronics COMMGR2 Enables Remote Code Execution
Key Takeaways CVSS v3.1 base score of 9.8 (Critical) with vector CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H, according to the CNA Delta Electronics COMMGR2 contains an out-of-bounds write vulnerability (CWE-787) enabling unauthenticated remote code execution NVD lists the vulnerability as analyzed; vendor advisory Delta-PCSA-2026-00005 is available addressing multiple COMMGR2 vulnerabilities No evidence of active exploitation in the wild; specific affected […]
When HttpOnly Isn’t Enough: Chaining XSS and GhostScript for Full RCE Compromise
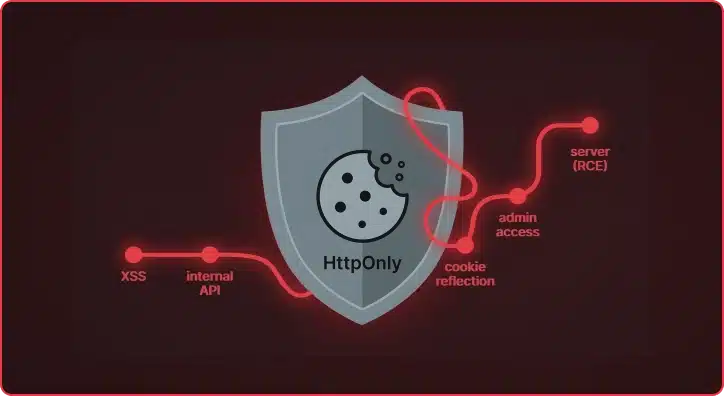
What started as a standard cross-site scripting vulnerability in a document processing platform turned into a full administrative takeover of the application and, ultimately, remote code execution on the underlying server. The HttpOnly flag protected the session cookie from Javascript, but did the application keep it safe? During a recent assessment of a document processing […]
Augustus v0.0.9: Multi-Turn Attacks for LLMs That Fight Back
Single-turn jailbreaks are getting caught. Guardrails have matured. The easy wins — “ignore previous instructions,” base64-encoded payloads, DAN prompts — trigger refusals on most production models within milliseconds. But real attackers don’t give up after one message. They have conversations. Augustus v0.0.9 now ships with a unified engine for LLM multi-turn attacks, with four distinct […]
Et Tu, RDP? Detecting Sticky Keys Backdoors with Brutus and WebAssembly

Everyone knows that one person on the team who’s inexplicably lucky, the one who stumbles upon a random vulnerability seemingly by chance. A few days ago, my coworker Michael Weber was telling me about a friend like this who, on a recent penetration test, pressed the shift key five times at an RDP login screen […]
Mapping the Unknown: Introducing Pius for Organizational Asset Discovery
Asset discovery is an essential part of Praetorian’s service delivery process. When we are engaged to carry out continuous external penetration testing, one key action is to build and maintain a thorough target asset inventory that goes beyond any lists or databases provided by the system owner. Pius is our open-source attack surface mapping tool […]
When Proxies Become the Attack Vectors in Web Architectures
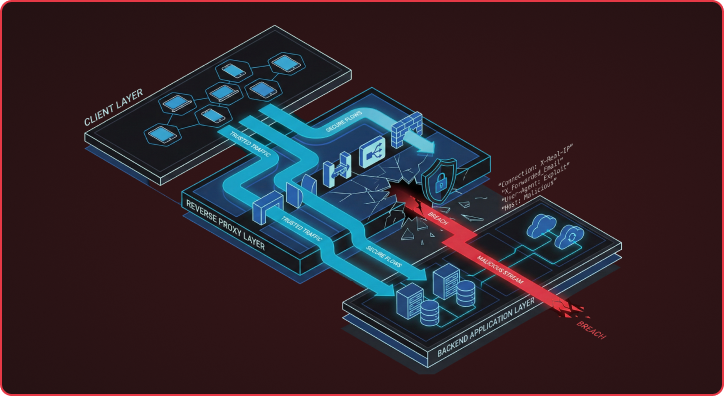
Many Reverse proxy attack vectors expose a flawed assumption in modern web architectures that backends can blindly trust security-critical headers from upstream reverse proxies. This assumption breaks down because HTTP RFC flexibility allows different servers to interpret the same headers in fundamentally different ways, creating exploitable gaps that attackers are increasingly targeting. I want to […]
Beyond Prompt Injection: The Hidden AI Security Threats in Machine Learning Platforms
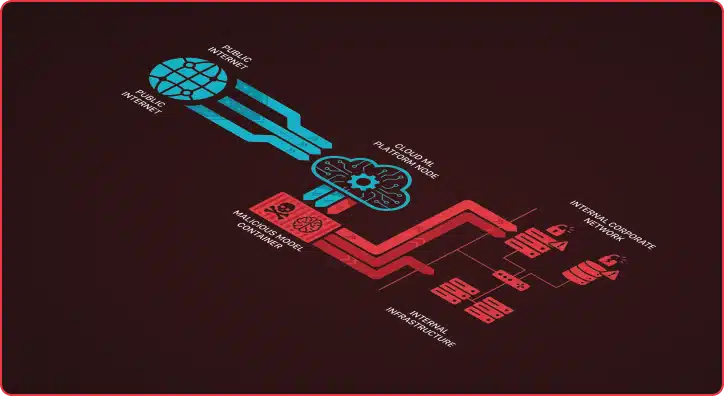
What’s the first thing you think of when you hear about AI attacks and vulnerabilities? If you’re like most people, your mind probably jumps to Large Language Model (LLM) vulnerabilities—system prompt disclosures, jailbreaks, or prompt injections that trick chatbots into revealing sensitive information or behaving in unintended ways. These risks have dominated headlines and security […]