Building Bridges, Breaking Pipelines: Introducing Trajan
TL;DR: Trajan is an open-source CI/CD security tool from Praetorian that unifies vulnerability detection and attack validation across GitHub Actions, GitLab CI, Azure DevOps, and Jenkins in a single cross-platform engine. It ships with 32 detection plugins and 24 attack plugins covering poisoned pipeline execution, secrets exposure, self-hosted runner risks, and AI/LLM pipeline vulnerabilities. It […]
How AI Agents Automate CVE Vulnerability Research

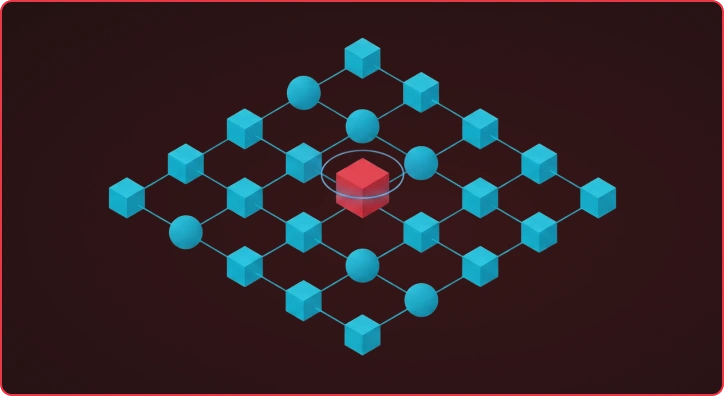
The CVE Researcher is a multi-agent AI pipeline that automates vulnerability research, detection template generation, and exploitation analysis. Built on Google’s Agent Development Kit (ADK), it coordinates specialized AI models through four phases — deep research, technology reconnaissance, actor-critic template generation, and exploitation analysis — to produce production-ready Nuclei detection templates overnight. Beyond Simple Automation […]
What’s Running on That Port? Introducing Nerva for Service Fingerprinting
Nerva is a high-performance, open-source CLI tool that identifies what services are running on open network ports. It fingerprints 120+ protocols across TCP, UDP, and SCTP, averaging 4x faster than nmap -sV with 99% detection accuracy. Written in Go as a single binary, Nerva helps security teams rapidly move from port discovery to service identification. […]
AI-Powered CVE Research: Winning the Race Against Emerging Vulnerabilities
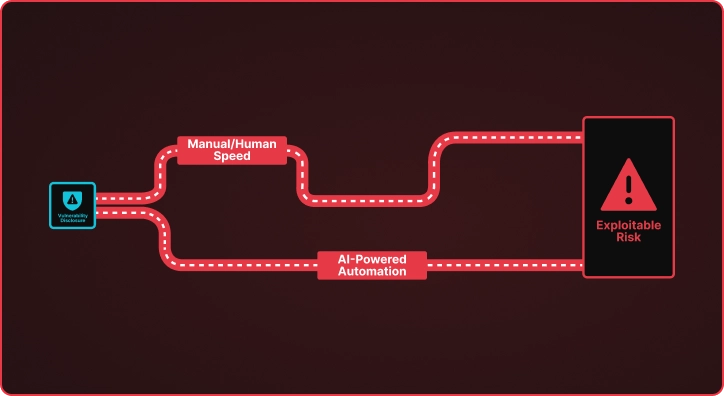
The Vulnerability Time Gap When CISA adds a new CVE to the Known Exploited Vulnerabilities catalog, a clock starts ticking. Security teams must understand the vulnerability, determine if they are exposed, and deploy detection mechanisms before adversaries weaponize the flaw. This process traditionally takes days or weeks of manual research by skilled security engineers who […]
Praetorian Guard finds critical flaws in OpenClaw – And What It Means for Your Software Supply Chain
At Praetorian, we’re constantly exploring how emerging technologies can strengthen security programs. Today, we’re sharing insights from our work building AI-powered vulnerability discovery capabilities within Praetorian Guard — finding critical security issues across the open-source ecosystem before they become public exploits. Using a multi-stage AI pipeline — automated discovery, validation, and exploit verification — we’ve […]
MCP Server Security: The Hidden AI Attack Surface
TL;DR – MCP servers – the integration layer connecting AI assistants to external tools and data – are a significant and underexplored attack surface. Our research demonstrates that both locally hosted and third-party MCP servers can be exploited to execute arbitrary code, exfiltrate sensitive data, and manipulate user behavior, often with zero indication to the […]
Julius Update: From 17 to 33 Probes (and Now Detecting OpenClaw)

TL;DR: Julius v1.2.0 nearly doubles probe coverage from 17 to 33, adding detection for self-hosted inference servers, AI gateways, and RAG/orchestration platforms like Dify, Flowise, and KoboldCpp. The headline addition is OpenClaw, a fast-growing AI agent gateway where exposed instances leak API keys, grant filesystem access, and allow full user impersonation. Update Julius and run […]
Et Tu, Default Creds? Introducing Brutus for Modern Credential Testing
It’s day three of staring at a spreadsheet of 700,000 live hosts. Your port scans are done. Fingerprintx has identified thousands of SSH services, databases, admin panels, and file shares across a sprawling enterprise network. Now comes the part that every penetration tester hates: auditing and testing credentials at scale. You need to check for […]
Gone Phishing, Got a Token: When Separate Flaws Combine

TL;DR: Two medium-severity flaws, an unsecured email API endpoint and verbose error messages exposing OAuth tokens, chain together to enable authenticated phishing that bypasses all email security controls, persistent access to Microsoft 365 environments, and full infrastructure compromise. Neither flaw alone would be critical; combined, they’re devastating. Modern web applications increasingly create attack surfaces through […]
Introducing Julius: Open Source LLM Service Fingerprinting
The Growing Shadow AI Problem Over 14,000 Ollama server instances are publicly accessible on the internet right now. A recent Cisco analysis found that 20% of these actively host models susceptible to unauthorized access. Separately, BankInfoSecurity reported discovering more than 10,000 Ollama servers with no authentication layer—the result of hurried AI deployments by developers under […]